Mastering Vigenere cipher decryption is an essential milestone for anyone studying the evolution of modern cybersecurity. For over three centuries, this specific algorithm was considered the holy grail of secret communication, completely baffling the world’s greatest mathematicians and military commanders. Before we can truly appreciate the complexity of modern digital encryption, we must understand how codebreakers finally dismantled this legendary polyalphabetic system.
As we demonstrated in our previous deep dive into frequency analysis and chi-square statistics, simple monoalphabetic substitution ciphers are mathematically doomed. Because human language relies on predictable linguistic structures, replacing letters with static symbols only creates an illusion of security. To survive the devastating logic of frequency analysis, cryptographers had to fundamentally change the rules of the game, creating a system where the letter ‘E’ could be encrypted as ‘X’ in the first sentence, but as ‘M’ or ‘Q’ in the next.
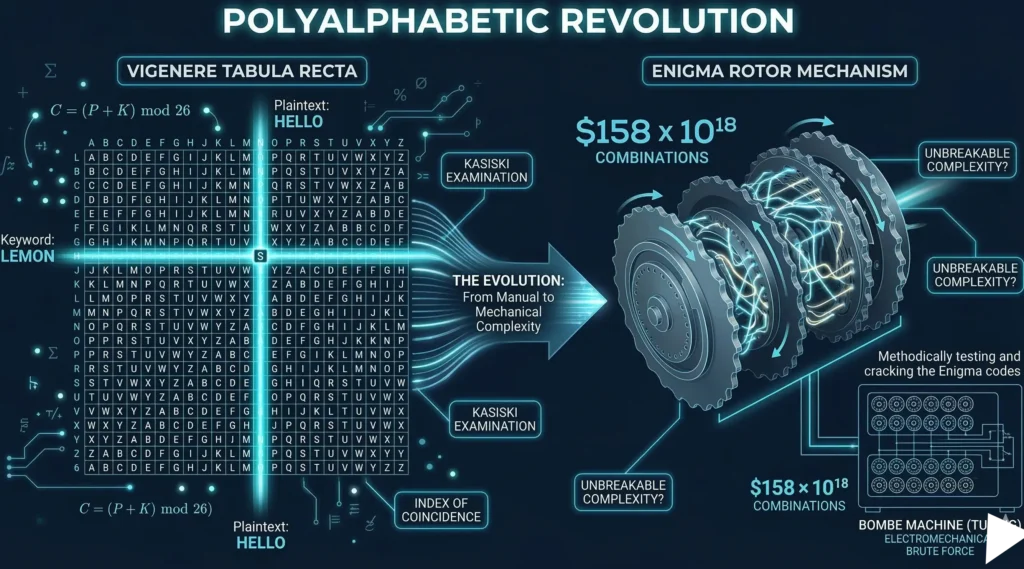
In this advanced cryptographic module, we will explore the mathematical revolution that temporarily defeated frequency analysis. We will break down the mathematics of the index of coincidence, see the Kasiski examination explained in practical terms, and dissect the ultimate mechanical manifestation of these concepts: Enigma machine cryptography.
In this advanced cryptographic module, we will explore the mathematical revolution that temporarily defeated frequency analysis. We will master the mechanics of Vigenere cipher decryption, break down the mathematics of the index of coincidence, see the Kasiski examination explained in practical terms, and dissect the ultimate mechanical manifestation of these concepts: Enigma machine cryptography.
1. The Foundation of Polyalphabetic Cipher Architecture
The prefix “poly-” means “many.” Unlike the Caesar cipher, which uses a single shifted alphabet to encrypt an entire message, a polyalphabetic cipher architecture uses multiple different substitution alphabets systematically. By rotating through different alphabets, the cryptographer actively flattens the frequency distribution of the ciphertext, destroying the statistical peaks and valleys that cryptanalysts rely on.
2. The Vigenère Cipher: “Le Chiffre Indéchiffrable”
Invented in the 16th century, the Vigenère cipher became the gold standard of polyalphabetic encryption. For over 300 years, it was widely referred to as le chiffre indéchiffrable (the indecipherable cipher).
The system relies on a Tabula Recta—a grid containing 26 different Caesar ciphers, each shifted by one additional letter. To encrypt a message, the sender and receiver agree on a secret keyword (e.g., “LEMON”). The keyword is repeated until it matches the length of the plaintext.
The Mathematics of Vigenère
While the Tabula Recta is a helpful visual tool, a modern cryptographer understands the Vigenère cipher through modular arithmetic. If we map the alphabet to integers from $0$ to $25$, the encryption function for the $i$-th letter of the plaintext ($P_i$) using the $i$-th letter of the keyword ($K_i$) is:
$$C_i = (P_i + K_i) \pmod{26}$$
Because the keyword changes the shift value for every single letter, standard frequency analysis is completely useless. The letter ‘E’ will be dispersed across multiple different ciphertext characters. So, how is Vigenere cipher decryption possible?
3. Kasiski Examination Explained: Finding the Key Length
The myth of the indecipherable cipher was shattered in 1863 by Friedrich Kasiski, a Prussian infantry officer. Kasiski realized that the Vigenère cipher has a fatal structural flaw: the keyword repeats.
If the keyword is “LEMON” (length 5), every 5th letter of the plaintext is encrypted using the exact same shift. Therefore, if a common English word like “THE” appears multiple times in the plaintext, and those appearances happen to align perfectly with the same letters of the keyword, they will produce the exact same ciphertext sequence.
The Kasiski examination explained step-by-step:
- Scan the ciphertext for repeating sequences of characters (typically 3 or more letters).
- Calculate the exact distance (number of letters) between these repeating sequences.
- Find the Greatest Common Divisor (GCD) of those distances.
If the distances between repeating sequences are 20, 35, and 50, the GCD is 5. The cryptanalyst can mathematically deduce that the secret keyword is exactly 5 letters long. Once the key length is known, the complex polyalphabetic cipher is shattered into 5 simple Caesar ciphers, which can be easily broken using standard frequency analysis.
4. The Mathematics of the Index of Coincidence
While Kasiski’s method is brilliant, it requires luck (repeating words must align with the keyword). In 1920, legendary American cryptographer William Friedman developed a purely statistical method to defeat polyalphabetic ciphers without relying on repeating sequences. This metric is called the index of coincidence (IoC).
The index of coincidence measures the probability that any two randomly selected letters from a text are identical. In a completely random string of letters, the probability is roughly $1/26 \approx 0.0385$. However, because standard English has a skewed distribution, the IoC of plain English text is significantly higher, mathematically proven to be approximately $0.0667$.
The mathematical formula for the IoC is:
$$IC = \frac{\sum_{i=A}^{Z} f_i(f_i – 1)}{N(N – 1)}$$
Where:
- $f_i$ = The frequency count of a specific letter in the text.
- $N$ = The total number of letters in the text.
During Vigenere cipher decryption, a cryptanalyst will divide the ciphertext into columns based on a guessed key length. They then calculate the IoC for each column. If the guessed key length is correct, each column is effectively a simple Caesar cipher, and its IoC will spike to $0.0667$. If the guess is wrong, the column remains polyalphabetic, and the IoC will hover near random ($0.0385$).
5. Python Implementation: Automating Vigenere Decryption
Let’s write a Python script that calculates the index of coincidence to mathematically detect the correct keyword length in a Vigenère ciphertext. This demonstrates how modern statistical attacks bypass human guessing entirely.
def calculate_ioc(text):
"""Calculates the Index of Coincidence for a given text."""
n = len(text)
if n <= 1:
return 0
# Count frequencies of each letter
counts = {chr(i + 65): 0 for i in range(26)}
for char in text:
if char.isalpha():
counts[char.upper()] += 1
# Apply the IoC formula: Sum(f * (f - 1)) / (N * (N - 1))
numerator = sum(f * (f - 1) for f in counts.values())
denominator = n * (n - 1)
return numerator / denominator
def find_key_length(ciphertext, max_length=10):
"""Finds the most probable Vigenere key length using IoC."""
# Clean the text
clean_text = ''.join(filter(str.isalpha, ciphertext.upper()))
print(f"{'Guessed Length':<15} | {'Average IoC'}")
print("-" * 35)
best_length = 0
best_ioc = 0
for length in range(1, max_length + 1):
# Extract columns based on guessed length
columns = ['' for _ in range(length)]
for i, char in enumerate(clean_text):
columns[i % length] += char
# Calculate average IoC for all columns
avg_ioc = sum(calculate_ioc(col) for col in columns) / length
print(f"{length:<15} | {avg_ioc:.4f}")
# If IoC approaches English standard (~0.066), we likely found the key length
if avg_ioc > best_ioc:
best_ioc = avg_ioc
best_length = length
print(f"\nMost probable key length: {best_length} (IoC: {best_ioc:.4f})")
# Example Usage
# Ciphertext encrypted with a 5-letter keyword
encrypted_data = "MOMUDGZWDYVVRVYQ..." # Truncated for example
find_key_length(encrypted_data)
6. The Ultimate Machine: Enigma Machine Cryptography
While the Vigenère cipher was broken by the late 19th century, the core concept of polyalphabetic cipher architecture evolved into military hardware. In the 20th century, engineers realized that the flaw of Vigenère was the repeating, static keyword. To fix this, they built electromechanical rotor machines.
The pinnacle of this era was Enigma machine cryptography, utilized by the German military during WWII. The Enigma machine was essentially a mechanical Vigenère cipher that changed its “keyword” after every single keystroke. By cascading multiple rotating wheels (rotors) and a plugboard, the machine possessed a staggering $158 \times 10^{18}$ possible initial states.
Because the internal wiring of the rotors physically altered the electrical path of every character, manual index of coincidence calculations were nearly impossible. It required the invention of the world’s first programmable computers—the Bombe machines, designed by Alan Turing at Bletchley Park—to perform electromechanical brute-forcing of the daily rotor settings.
7. Conclusion: The Polyalphabetic Legacy
The history of Vigenere cipher decryption and the fall of the Enigma machine prove that shifting alphabets, no matter how complex the mechanical rotors become, ultimately leave statistical fingerprints. If a cryptographic system has a repeating pattern or relies on deterministic shifts, mathematics will find a way to break it.
In our final module on classical cryptography, we will ask the ultimate question: Is there a cipher that produces an Index of Coincidence of exactly $0.0385$, has absolutely zero repeating sequences, and is mathematically proven to be unbreakable? The answer is yes. Next, we explore the theoretical perfection of the One-Time Pad.
Bądź na bieżąco!
Zapisz się, aby nie przegapić nowości na Review Space.
Join Our Newsletter
No spam. Unsubscribe anytime.