To understand modern symmetric block ciphers, we must first accept the harsh reality of the internet: perfect mathematical security is logistically impossible. As we discovered in our deep dive into One-Time Pad cryptography, achieving absolute perfect secrecy requires securely distributing massive, truly random keys. Because we cannot ship hard drives full of keys to every web server we visit, modern cryptography relies on a different concept: computational security.
Instead of making a cipher mathematically impossible to break, we make it computationally unfeasible. We design algorithms so complex that it would take the world’s fastest supercomputers billions of years to guess the key. This shift in philosophy gave birth to modern encryption, where the same secret key is used to both lock and unlock the data.
In this comprehensive guide to symmetric block ciphers, we will explore the foundational principles of Shannon confusion and diffusion, dissect the rise and fall of the Data Encryption Standard (DES), and perform a deep architectural breakdown of the undisputed king of modern cryptography: the Advanced Encryption Standard (AES).
1. The Foundation of Symmetric Block Ciphers: Confusion and Diffusion
In 1945, the father of Information Theory, Claude Shannon, published a classified report that defined the two mandatory properties for any secure symmetric block ciphers: Confusion and Diffusion.
- Confusion: This principle dictates that the relationship between the secret key and the ciphertext must be as complex and non-linear as possible. If a cryptanalyst intercepts the ciphertext, they should not be able to deduce any mathematical patterns that lead back to the key. This is typically achieved through complex substitution tables (S-boxes).
- Diffusion: This principle requires that the statistical structure of the plaintext be dissipated into long-range statistics of the ciphertext. In practical terms: changing a single bit of the plaintext should change approximately 50% of the ciphertext bits. This creates an avalanche effect, completely destroying any statistical frequency analysis.
Every algorithm we discuss below is essentially a machine designed to maximize Shannon’s confusion and diffusion.
2. Data Encryption Standard (DES) & The Feistel Network
When studying the history of symmetric block ciphers, we must look back to the 1970s. As computers entered the commercial banking sector, the world needed a standardized encryption algorithm. IBM developed a cipher called Lucifer, which, after modifications by the NSA, became the Data Encryption Standard (DES) in 1977.
DES is built on a brilliant architectural concept called a Feistel network. Instead of trying to encrypt the entire block of data at once, a Feistel network splits the 64-bit plaintext block into two 32-bit halves: Left ($L_0$) and Right ($R_0$).
In each round of encryption (DES uses 16 rounds), the Right half is passed through a complex mathematical function ($F$) using a subkey ($K_i$). The result is then XORed ($\oplus$) with the Left half. The two halves are then swapped for the next round. The mathematical beauty of the Feistel structure is that the $F$ function doesn’t even need to be reversible for decryption to work!
$$L_{i+1} = R_i$$
$$R_{i+1} = L_i \oplus F(R_i, K_i)$$
The Fall of DES
While the Feistel network DES architecture was incredibly robust against statistical attacks, the NSA forced IBM to reduce the key size to just 56 bits. In 1977, 56 bits seemed secure. By 1998, a machine built by the Electronic Frontier Foundation (EFF) called “Deep Crack” brute-forced a DES key in just 56 hours. DES was officially dead.
3. The Band-Aid Solution: Triple DES (3DES)
Banks and governments had billions of dollars invested in legacy hardware. They needed an immediate fix that didn’t require designing a whole new algorithm. The solution was Triple DES (3DES).
Instead of encrypting the data once, 3DES runs the DES algorithm three times using three different keys ($K_1$, $K_2$, $K_3$). To maintain backward compatibility with old hardware, the sequence was cleverly designed as Encrypt-Decrypt-Encrypt (EDE):
$$Ciphertext = E_{K3}(D_{K2}(E_{K1}(Plaintext)))$$
While 3DES effectively mitigated the brute-force threat, it was incredibly slow and inefficient in software. The world desperately needed a cipher designed for the 21st century.
4. The King is Crowned: Advanced Encryption Standard (AES)
In 2001, after a fierce 5-year global competition, the National Institute of Standards and Technology (NIST) selected the Rijndael cipher, created by Belgian cryptographers Joan Daemen and Vincent Rijmen, to become the Advanced Encryption Standard (AES). It quickly became the absolute gold standard for symmetric block ciphers worldwide.
Unlike DES, AES does not use a Feistel network. It uses a Substitution-Permutation Network (SPN). It processes data in 128-bit blocks, organizing the data into a $4 \times 4$ grid of bytes called the State array. Depending on the key size (128, 192, or 256 bits), AES applies 10, 12, or 14 rounds of intense mathematical transformations.
5. Inside the AES Encryption Architecture
A single round of AES consists of four distinct transformations. Together, they create a perfect storm of confusion and diffusion.
Step 1: SubBytes (Confusion)
Every byte in the State array is substituted with a different byte using a pre-calculated lookup table (the Rijndael S-box). This is a highly non-linear transformation based on calculating the multiplicative inverse in the Galois Field $GF(2^8)$. This step provides the core cryptographic confusion, ensuring the cipher resists differential and linear cryptanalysis.
Step 2: ShiftRows (Diffusion)
The bytes in the State array are physically shifted. The first row remains unchanged. The second row shifts 1 position to the left. The third row shifts 2 positions, and the fourth row shifts 3 positions. This simple permutation ensures that the columns of data are thoroughly mixed in the next step.
Step 3: MixColumns (Diffusion)
This is the mathematical heavy lifter for diffusion. Each column of the State array is multiplied by a fixed polynomial matrix in $GF(2^8)$. If you change just one bit entering this step, all four output bytes will change entirely.
$$ \begin{bmatrix} r_0 \\ r_1 \\ r_2 \\ r_3 \end{bmatrix} = \begin{bmatrix} 2 & 3 & 1 & 1 \\ 1 & 2 & 3 & 1 \\ 1 & 1 & 2 & 3 \\ 3 & 1 & 1 & 2 \end{bmatrix} \begin{bmatrix} a_0 \\ a_1 \\ a_2 \\ a_3 \end{bmatrix} $$
Step 4: AddRoundKey
Finally, the entire State array is XORed with a 128-bit Round Key. Where do these round keys come from? Before encryption begins, AES uses a Key Expansion algorithm to stretch your original 256-bit key into fifteen distinct 128-bit subkeys—one for each round, plus an initial one.
The Synergy of the AES Architecture
When you analyze these four steps collectively, the true brilliance of the AES encryption architecture is revealed. It is the ultimate manifestation of Shannon confusion and diffusion. The SubBytes, ShiftRows, MixColumns, and AddRoundKey functions are not arbitrary math; they work as a tightly coupled engine. SubBytes destroys linear relationships between the plaintext and the key (perfect confusion). Meanwhile, ShiftRows and MixColumns guarantee that after just two complete rounds, every single bit of the ciphertext depends mathematically on every single bit of the plaintext (perfect diffusion). This absolute “avalanche effect” is what makes AES seemingly invincible to both differential and linear cryptanalysis.
6. Symmetric Block Ciphers: Modes of Operation
While symmetric block ciphers like AES can perfectly encrypt a 128-bit block, what if you want to encrypt a 10-Gigabyte video file? You must break the file into millions of 128-bit blocks and use a mode of operation to stitch them together securely.
Electronic Codebook (ECB) – The Fatal Mistake
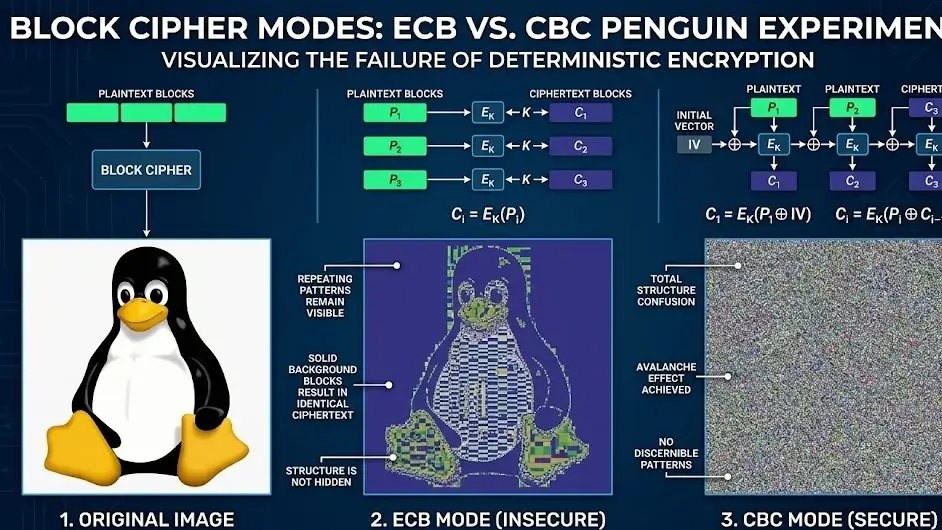
The simplest mode is ECB. You encrypt Block 1, then Block 2, then Block 3, all independently using the exact same key. This is a catastrophic security failure. Because AES is deterministic, identical plaintext blocks will always produce identical ciphertext blocks.
To truly understand the critical importance of secure block cipher modes of operation, cryptography professors often point to the famous “ECB Penguin” experiment. If you take an uncompressed bitmap image of Tux (the Linux mascot) and encrypt it using ECB mode, the resulting ciphertext image still clearly displays the visual outline of the penguin. Why? Because the solid background pixels of the original image are grouped into identical blocks, and ECB turns them into identical encrypted blocks. It completely fails to hide the underlying structural patterns of the data, proving that even a flawless algorithm like AES is easily compromised if deployed with a naive operational mode.
Cipher Block Chaining (CBC)
To fix ECB’s flaw, CBC introduces an Initialization Vector (IV). Before encrypting the first plaintext block, it is XORed with the random IV. The resulting ciphertext block is then XORed with the next plaintext block before encryption. This creates a chain reaction where every block depends on all previous blocks. Identical plaintexts now produce completely different ciphertexts.
Galois/Counter Mode (GCM) – The Modern Standard
While CBC is secure, it cannot be parallelized (you must wait for Block 1 to finish before encrypting Block 2), making it slow on modern multi-core processors. Today, the absolute gold standard for internet traffic (HTTPS, TLS 1.3) is AES-GCM.
GCM turns the block cipher into a stream cipher by encrypting an incrementing counter rather than the data itself. Furthermore, it incorporates an authentication tag using Galois field multiplication, proving not only that the data is encrypted, but also that no hacker has tampered with it in transit.
Conclusion
Symmetric block ciphers like AES are the undisputed workhorses of modern cybersecurity. With an architecture utilizing non-linear S-boxes and intense matrix multiplication, AES-256 provides a level of computational security that even theoretical quantum computers cannot easily break.
However, symmetric block ciphers still suffer from one fundamental flaw: both parties must somehow agree on the secret key before encryption can begin. How do you securely share an AES key across a hostile internet with a server you’ve never spoken to before? In our next module, we will explore the magic of Public Key Cryptography and the RSA algorithm, the mathematical breakthrough that made the modern internet possible.
Bądź na bieżąco!
Zapisz się, aby nie przegapić nowości na Review Space.
Join Our Newsletter
No spam. Unsubscribe anytime.