When analyzing the evolution of secure digital communications, modern engineers often overlook the foundational lessons of the past. Long before the invention of AES-256, elliptic curves, or quantum-resistant algorithms, military commanders relied on the fundamental mathematics of historical cryptography. At the core of every ancient encryption system lies a fundamental architectural decision: should we change the letters themselves, or should we merely change their positions?
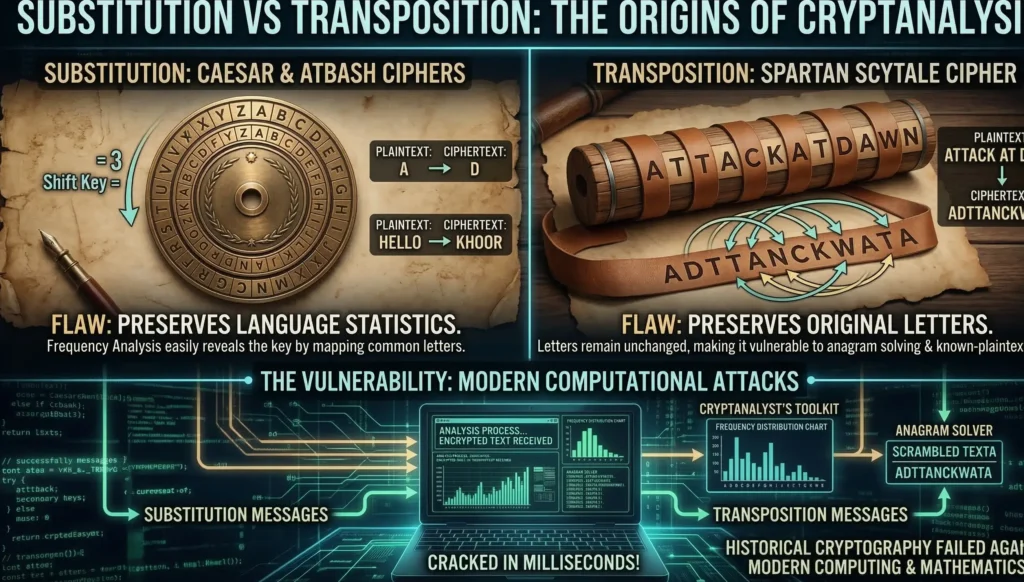
This critical debate between a substitution vs transposition cipher forms the absolute bedrock of modern cryptographic theory. Every time an ancient empire developed a “perfect” system to hide their military orders, brilliant mathematicians eventually found a fatal structural flaw, giving birth to the science of cryptanalysis.
In this comprehensive guide, we will journey to the origins of encryption. We will dissect the exact mathematical principles that governed the ancient world, explore the mechanics of Caesar cipher modular arithmetic, decode the ancient Hebrew Atbash cipher algorithm, and examine the mechanical genius behind Spartan Scytale cryptography. Finally, we will write a Python script to demonstrate just how easily modern computers can shatter these historic defenses.
1. The Foundation of Historical Cryptography
Before the digital age, cryptography was entirely manual. Cryptographers had to design systems that were mathematically complex enough to confuse intercepting enemies, yet simple enough that a general in the middle of a battlefield could encrypt and decrypt messages using only pen and paper. If you want to understand the profound physical evolution of these systems, the Crypto Museum’s extensive archive on historical cryptography provides incredible evidence of how ancient empires fought their secret wars.
To achieve secure communication, early cryptographers divided their strategies into two distinct mathematical categories. Understanding the mechanical differences in a substitution vs transposition cipher is essential because modern algorithms like AES actually combine both of these historic techniques. As we discussed in our advanced guide on AES S-box mathematics, modern ciphers use substitution for “confusion” and transposition for “diffusion”. Let’s isolate and examine how these techniques worked in their pure, ancient forms.
2. Substitution Ciphers: The Mathematics of Replacement
In a substitution cipher, the positions of the letters remain exactly the same, but the identity of the letters is changed. The plaintext letter is systematically replaced by a different letter, number, or symbol according to a specific mathematical rule. The visual meaning of the data is destroyed, even though the underlying grammatical structure remains intact.
Caesar Cipher Modular Arithmetic
The most famous implementation of a substitution cipher was utilized by Julius Caesar to protect the military communications of the Roman Empire. The Caesar cipher is a monoalphabetic substitution system based on a simple, fixed alphabetical shift.
While Caesar supposedly used a shift of three (where ‘A’ becomes ‘D’, ‘B’ becomes ‘E’, etc.), the true genius of the system lies in its mathematical representation. Today, we understand this system through the lens of Caesar cipher modular arithmetic.
If we map the standard English alphabet to a numerical index from $0$ to $25$ (where $A=0, B=1, \dots, Z=25$), we can mathematically define the encryption function $E$ for a plaintext letter $P$ using a secret shift key $K$:
$$C = (P + K) \pmod{26}$$
To reverse the process, the recipient uses the decryption function $D$, subtracting the key from the ciphertext letter $C$:
$$P = (C – K) \pmod{26}$$
The modulo operation ($\pmod{26}$) ensures that if the shift goes past the letter ‘Z’, it automatically wraps around back to ‘A’. While this application of Caesar cipher modular arithmetic was practically unbreakable to illiterate ancient tribes, it possesses a fatal cryptographic flaw: a severely limited keyspace. Because the English alphabet only has 26 letters, there are only 25 possible shift keys. An attacker can simply test all 25 variations in a matter of minutes to reveal the hidden message.
The Atbash Cipher Algorithm
Predating the Roman Empire, the Atbash cipher is an ancient Hebrew substitution cipher found in biblical texts. Unlike the Caesar cipher, which shifts the alphabet forward, the Atbash cipher algorithm folds the alphabet entirely in half, creating a perfect mirror reflection.
In the English equivalent of Atbash, the first letter ‘A’ is replaced by the last letter ‘Z’. The second letter ‘B’ is replaced by the second-to-last letter ‘Y’, and so on.
Mathematically, using our $0$ to $25$ alphabetical index, the Atbash cipher algorithm can be defined as:
$$C = 25 – P$$
The fatal flaw of the Atbash system is that it completely violates what we now call Kerckhoffs’s Principle. Auguste Kerckhoffs stated that a cryptographic system must remain secure even if everything about the system, except the key, is public knowledge. The Atbash cipher algorithm has no key. The algorithm itself is the secret. Once an attacker discovers that Atbash is being used, the encryption is instantly broken, as there is no variable key to guess.
Because the Atbash cipher algorithm lacks a variable key, it is completely deterministic. In modern cybersecurity, as we learned in our deep dive into Shannon Entropy and TRNGs, deterministic systems without random keys are fundamentally broken. The absolute predictability of the Atbash cipher algorithm makes it a fascinating piece of historical cryptography, but entirely useless for dynamic military communication.
3. Transposition Ciphers: The Art of Rearrangement
When comparing a substitution vs transposition cipher, we observe a radical shift in philosophy. A transposition cipher does not alter the identity of the letters at all. Instead, it radically scrambles their positions. If you intercept a transposed message, you possess all the correct letters of the plaintext, but they are mixed into a meaningless anagram.
Scytale Cryptography: The First Military Hardware
The earliest known physical device used for military cryptography was developed by the ancient Spartans around 400 BC. It was called the Scytale (pronounced sit-ah-lee), and it represents a brilliant mechanical implementation of a transposition cipher.
Scytale cryptography relied on a wooden cylinder of a very specific, carefully measured diameter. The sender would take a long, narrow strip of parchment or leather and wrap it tightly around the cylinder in a spiral. They would then write their message horizontally across the adjacent wraps of the parchment.
When the parchment was unwound from the cylinder, the letters appeared as a completely random, meaningless vertical sequence. The genius of Scytale cryptography is that the wooden cylinder itself acts as the cryptographic key. The message could only be decrypted if the receiving general possessed a cylinder of the exact same diameter. When wrapped around the correct cylinder, the letters would perfectly realign, revealing the horizontal plaintext.
Mathematically, the Scytale is an ancient form of a “Columnar Transposition Cipher.” The circumference of the cylinder dictates the length of the columns. If the intercepting enemy captured the parchment, they would have to guess the correct column length (cylinder diameter) to read the text. However, just like the Caesar cipher, the number of practical cylinder diameters is relatively small, making it highly vulnerable to systemic brute-forcing.
When studying the physical mechanics of Scytale cryptography, it becomes clear why it was favored by military generals: it was remarkably fast and required absolutely no mathematical calculations like the Caesar cipher modular arithmetic did. However, because Scytale cryptography merely rearranged existing letters without altering their identity, a persistent attacker could simply wrap the captured parchment around differently sized wooden rods until the horizontal message naturally materialized, bypassing the cipher entirely.
4. Analyzing the Substitution vs Transposition Cipher Dilemma
When studying historical cryptography, evaluating the substitution vs transposition cipher reveals that both methods, in their pure forms, are fundamentally flawed when used in isolation.
- Substitution Flaw: By changing the letters but keeping the positions, monoalphabetic substitution preserves the exact statistical frequency of the underlying language. If the letter ‘E’ is the most common letter in English, its substituted ciphertext equivalent will also be the most common symbol in the encrypted text.
- Transposition Flaw: By moving letters but keeping their original identities, transposition preserves the exact letters used. If the message contains the word “ATTACK”, the ciphertext will always contain two ‘A’s, two ‘T’s, one ‘C’, and one ‘K’. An attacker can use anagram-solving techniques and linguistic bigram/trigram frequencies to reconstruct the message.
Modern encryption algorithms, recognizing these historical failures, combine both approaches. They use Substitution to destroy linguistic frequencies (Confusion) and Transposition to spread changes across the entire data block (Diffusion).
5. Practical Application: Brute-Forcing Caesar in Python
To demonstrate the fragility of historical cryptography, let’s look at how modern computational power trivializes ancient defenses. Because Caesar cipher modular arithmetic only utilizes 25 possible keys, we do not need advanced mathematics to break it. We can simply write a Python script that iterates through every possible shift and prints the result, allowing our eyes to instantly pick out the English plaintext.
def brute_force_caesar(ciphertext: str):
"""
Performs a brute-force attack on a Caesar cipher by
calculating all 25 possible modular shifts.
"""
print(f"--- Initiating Brute Force Attack ---")
print(f"Ciphertext: {ciphertext}\n")
# Iterate through all possible keys (1 to 25)
for key in range(1, 26):
decrypted_text = ""
for char in ciphertext:
# Check if character is an uppercase letter
if char.isupper():
# Apply Caesar cipher modular arithmetic: P = (C - K) mod 26
# ord('A') is 65 in ASCII
shifted = (ord(char) - 65 - key) % 26
decrypted_text += chr(shifted + 65)
# Check if character is a lowercase letter
elif char.islower():
# ord('a') is 97 in ASCII
shifted = (ord(char) - 97 - key) % 26
decrypted_text += chr(shifted + 97)
# If it's a space or punctuation, leave it unchanged
else:
decrypted_text += char
print(f"Key {key:02d}: {decrypted_text}")
# Example Usage:
# The ciphertext below is encrypted with an unknown Caesar shift.
secret_message = "Khoor, Zruog! Wklv lv d whvw ri wkh fdhvdu flskhu."
brute_force_caesar(secret_message)
If you run this script, it will instantly print 25 different sentences. At Key 03, the output will clearly read: “Hello, World! This is a test of the caesar cipher.” What once protected the secrets of the Roman Empire can now be broken in less than a millisecond by five lines of Python code.
6. Conclusion: The Birth of Cryptanalysis
The study of historical cryptography teaches us that absolute security is an illusion if the underlying mathematical structure is too simple. The substitution vs transposition cipher debate laid the groundwork for secure communications, but both methods ultimately fell to the relentless logic of human ingenuity.
While a simple Python script can brute-force the 25 keys of a Caesar cipher, what happens when the key space is too large to brute-force? In the 9th century, Arab mathematicians discovered a way to break substitution ciphers without guessing the key at all, by exploiting the mathematical predictability of human language itself.
In our next module, we will explore the devastation of Frequency Analysis and discover how Zipf’s Law and statistical probability forever changed the landscape of cryptanalysis.
Bądź na bieżąco!
Zapisz się, aby nie przegapić nowości na Review Space.
Join Our Newsletter
No spam. Unsubscribe anytime.