Finite Field Arithmetic: How Computers Add and Multiply Bytes
At the core of every secure digital communication—whether you are connecting to a banking server, sending an encrypted message, or compiling a smart contract—lies a mathematical engine that the average programmer rarely sees. We tend to think of computer processors as massive calculators performing standard addition, subtraction, and multiplication. But in the realm of cryptography, standard mathematics is actually a severe vulnerability.
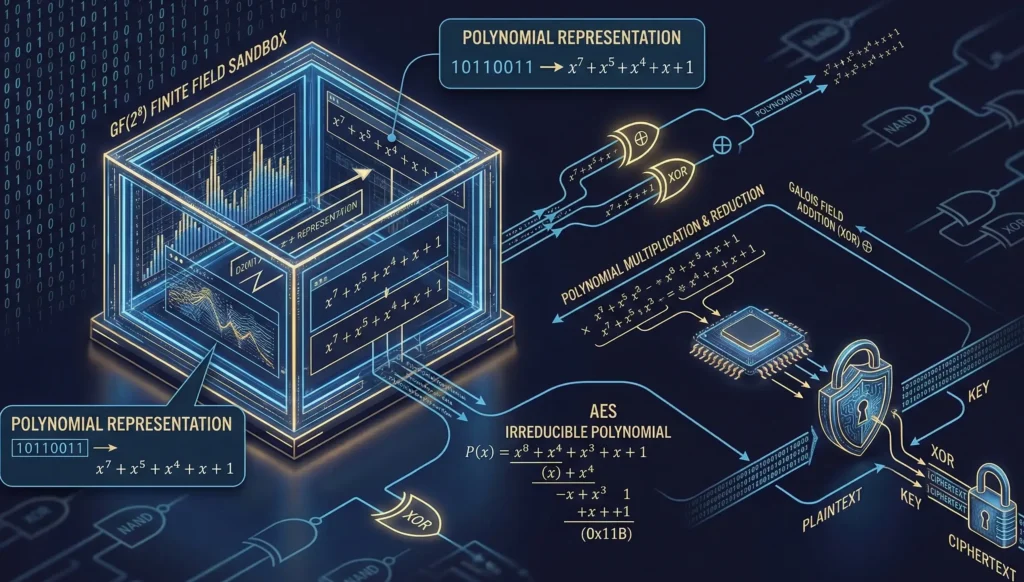
To secure data, modern encryption algorithms abandon regular numbers entirely. Instead, they rely on a strictly bounded, flawless mathematical sandbox. Understanding this sandbox requires a deep dive into operations in finite fields. When a processor encrypts a block of data, it is not multiplying numbers; it is manipulating mathematical polynomials using hardware-level logic gates.
In this comprehensive technical guide, we will break down the exact mechanics of finite field arithmetic. We will explore how an 8-bit byte is translated into an algebraic equation, why addition in Galois field is functionally identical to the famous bitwise XOR operation, and how polynomial arithmetic allows computers to multiply data without ever causing a memory overflow. Finally, we will write pure Python code to implement these cryptographic math operations from scratch.
1. The Problem with Standard Arithmetic in Computing
To appreciate the elegance of finite fields, we must first understand why standard arithmetic fails in cryptographic engineering.
Imagine you are writing a C++ or Python script to encrypt a single byte of data. A byte can hold values from 0 to 255. If your encryption algorithm multiplies the plaintext byte 150 by a secret key byte 4, the result is 600.
The number 600 cannot fit inside an 8-bit register. The computer experiences an integer overflow. In standard programming, you might solve this by allocating a larger variable type, like a 16-bit or 32-bit integer. But in cryptography, data must remain a fixed size. If a 1-megabyte file doubles in size every time it passes through a cryptographic round, it would quickly consume all available RAM and bandwidth.
Furthermore, we need mathematical operations to be reversible (so we can decrypt the data) and strictly non-linear (so hackers cannot guess the key using statistical patterns). Standard division leaves fractions, which destroy data precision. We need a closed mathematical loop.
2. The Solution: Introduction to GF(2⁸)
The solution to the overflow problem is a Galois Field, specifically the field denoted as $GF(2^8)$. In this mathematical universe, there are exactly 256 elements (from 0 to 255). No matter what operations you perform—addition, subtraction, multiplication, or division—the answer will always be a whole number between 0 and 255.
To make operations in finite fields work on a computer architecture, we must stop looking at a byte as a decimal number. Instead, we must view it as an array of binary bits, where each bit represents a coefficient in polynomial arithmetic.
Let’s take the binary byte 10110011 (which is 0xB3 in hexadecimal or 179 in decimal). In a finite field, we map each bit to a power of an unknown variable x, starting from x⁷ down to x⁰:
$$1x^7 + 0x^6 + 1x^5 + 1x^4 + 0x^3 + 0x^2 + 1x^1 + 1x^0$$
By removing the terms with a coefficient of 0, we get the final polynomial representation of our byte:
$$x^7 + x^5 + x^4 + x + 1$$
This is the secret language of cryptographic processors. From this point forward, the CPU is no longer dealing with integers; it is calculating polynomials where every coefficient is strictly a 0 or a 1.
3. Addition in Galois Field: The Magic of XOR
How do we add two bytes together using polynomial arithmetic? Let’s take two bytes, convert them to polynomials, and add them algebraically.
Byte A: 01010111 (Polynomial: x⁶ + x⁴ + x² + x + 1)
Byte B: 10010011 (Polynomial: x⁷ + x⁴ + x + 1)
If we add them like we would in a high school algebra class, we group the matching terms:
$$x^7 + x^6 + (1+1)x^4 + x^2 + (1+1)x + (1+1)$$
Here is where the magic of the finite field base-2 kicks in. Because our field is strictly base-2, the coefficients themselves are subject to modulo 2 arithmetic. In modulo 2, the number 2 does not exist. If you add 1 + 1, the result wraps around back to 0.
Therefore, every term with a coefficient of 2 is instantly erased from the equation:
$$x^7 + x^6 + x^2$$
If we convert this back to binary, we get 11000100. Now, let’s look at what just happened from a hardware perspective. If you look closely at modulo 2 addition, the rules are:
Step 1:
0 + 0 = 0
Step 2:
0 + 1 = 1
Step 3:
1 + 0 = 1
Step 4:
1 + 1 = 0
Any computer engineer will instantly recognize this truth table. It is the exact definition of the bitwise Exclusive-OR (XOR) gate. This means that addition in Galois field does not require a complex CPU Arithmetic Logic Unit (ALU) operation. The computer simply executes a native XOR hardware instruction, which takes less than a single clock cycle to complete.
Because subtraction in modulo 2 yields the exact same truth table as addition (since 1 – 1 = 0 and 0 – 1 = 1 modulo 2), addition and subtraction in a Galois Field are the exact same operation. In C++ or Python, adding two polynomials in $GF(2^8)$ is simply written as A ^ B.
4. XOR Encryption: The Unbreakable Foundation
Understanding that field addition is just XOR unlocks the concept of XOR encryption. XOR possesses a fascinating, perfectly symmetric property: if you XOR a piece of data with a key, you get a scrambled ciphertext. If you take that ciphertext and XOR it again with the exact same key, the key mathematically cancels itself out, leaving you with the original plaintext.
$$A \oplus B = C$$
$$C \oplus B = A$$
This property is the mathematical heartbeat of the One-Time Pad (OTP)—the only encryption algorithm ever mathematically proven to be 100% unbreakable. In a One-Time Pad, you take a plaintext message and XOR it bit-by-bit with a truly random key of the exact same length.
Because of the rules of modulo 2 addition, the resulting ciphertext is statistically perfectly flat. Even if an attacker has a quantum computer, they cannot crack XOR encryption in an OTP scenario, because every single possible plaintext is equally probable depending on what the key might have been.
Modern stream ciphers (like ChaCha20) and block ciphers (like AES) rely heavily on this. While they don’t have keys as long as the message, they use complex algorithms to generate massive streams of pseudo-random bytes, which are then rapidly added to the plaintext using Galois field addition (XOR) to secure the payload.
5. The Complexity of Finite Field Multiplication
While addition is trivial, multiplying two bytes in a finite field introduces a significant challenge. Unlike addition, polynomial multiplication causes the powers of x to increase.
Let’s multiply the byte 00000010 (which is just x) by the byte 10000000 (which is x⁷):
$$x \cdot x^7 = x^8$$
We immediately hit a wall. An 8-bit byte only has room for bits from x⁰ up to x⁷. The x⁸ term represents a 9th bit. This is the dreaded memory overflow. To keep operations in finite fields strictly within 8 bits, mathematicians use an irreducible polynomial.
An irreducible polynomial is a polynomial that cannot be factored into smaller polynomials—it acts exactly like a prime number in standard arithmetic. Just as clock math wraps around the number 12, polynomial arithmetic in $GF(2^8)$ wraps around this prime polynomial.
The Advanced Encryption Standard (AES) uses this specific irreducible polynomial:
$$P(x) = x^8 + x^4 + x^3 + x + 1$$
In hexadecimal notation, this is written as 0x11B. The rule of finite field multiplication is simple: multiply the two polynomials normally. If the degree of the resulting polynomial is 8 or higher, divide the result by P(x) using polynomial long division, and keep only the remainder. The remainder is guaranteed to fit perfectly back into 8 bits.
6. The Hardware Solution: The xtime Algorithm
Performing polynomial long division at runtime is incredibly slow. To optimize this, CPU designers implement a clever algorithm called xtime. The xtime function represents multiplying a polynomial by x (which is the decimal number 2).
In binary, multiplying a number by 2 simply means shifting all the bits to the left by one position. So, the first step of xtime is a native bitwise Left-Shift (<< 1).
However, we must check for overflow. Before shifting, we look at the most significant bit (the far-left bit, or x⁷). If this bit is a 0, shifting left is perfectly safe. But if this bit is a 1, shifting it left will push it into the 9th position (creating the forbidden x⁸).
If that happens, the computer completes the shift, and then immediately XORs the result with the lower 8 bits of the irreducible polynomial (which is x⁴ + x³ + x + 1, or 0x1B in hex). This XOR instantly reduces the 9th bit back down to zero while scattering the remainder mathematically across the lower bits.
Every complex multiplication in AES is built by chaining these simple xtime shifts and XOR additions together.
7. Deep Mathematical Proof: Polynomial Long Division in GF(2)
To truly master operations in finite fields, we must look at the exact mathematical proof of why modular reduction works. When programmers use the xtime bit-shift, they are actually performing a highly optimized hardware version of polynomial arithmetic known as polynomial long division.
Let’s assume a multiplication operation results in the term x9. As we know, an 8-bit byte cannot store this. We must divide x9 by our irreducible AES polynomial, P(x) = x8 + x4 + x3 + x + 1, and find the remainder.
In standard algebra, division is a long process of subtraction. But remember, addition in Galois field is mathematically identical to subtraction (both are executed via XOR logic gates). Therefore, to “subtract” P(x) from our oversized polynomial, we simply add them together.
First, we must mathematically isolate x8. If we take our irreducible polynomial and set it to zero (since we are finding the roots in the field modulo P(x)), we get:
$$x^8 + x^4 + x^3 + x + 1 = 0$$
Using the rules of addition in Galois field, we can move all terms except x8 to the right side of the equation. Because addition and subtraction are the exact same XOR operation, the signs do not change to negative (there are no negative numbers in this finite field):
$$x^8 = x^4 + x^3 + x + 1$$
This is a profound mathematical absolute. In our specific GF(28) universe, the 9th bit (x8) is perfectly mathematically equivalent to the polynomial x4 + x3 + x + 1 (which is exactly 0x1B in hexadecimal). Now, let’s solve for x9 using pure polynomial arithmetic substitution:
Step 1:
Rewrite the oversized term x9 as a product of x and x8.
$$x^9 = x \cdot (x^8)$$
Step 2:
Substitute our known absolute formula for x8 into the equation.
$$x^9 = x \cdot (x^4 + x^3 + x + 1)$$
Step 3:
Distribute the x across the substituted polynomial.
$$x^9 = x^5 + x^4 + x^2 + x$$
Look at what we just achieved! We successfully reduced a 10-bit value (x9) back into a safe 8-bit value without losing a single drop of cryptographic entropy. The resulting polynomial perfectly fits inside a standard computer byte (00110110 in binary).
By executing these strict operations in finite fields, algorithms like AES guarantee that XOR encryption never suffers from data loss, memory corruption, or fractional rounding errors. This exact mathematical substitution is what the C++ or Python code calculates behind the scenes during every single encryption cycle.
8. Deep Analysis: Python Implementation of GF(2⁸)
To fully master operations in finite fields, we must write the code. Below is a highly optimized, constant-time Python implementation of both addition and multiplication in $GF(2^8)$.
Notice that we never use standard operators like + or *. Everything is achieved through bitwise logic.
class GaloisField256:
"""A class to handle finite field arithmetic in GF(2^8) for cryptography."""
# The AES irreducible polynomial: x^8 + x^4 + x^3 + x + 1 (0x11B)
# We only need the lower 8 bits (0x1B) for the XOR reduction
REDUCTION_POLYNOMIAL = 0x1B
@staticmethod
def add(a: int, b: int) -> int:
"""
Addition in Galois field is simply a bitwise XOR.
Subtraction is identical to addition.
"""
return a ^ b
@staticmethod
def multiply(a: int, b: int) -> int:
"""
Multiplies two polynomials in GF(2^8) using the peasant multiplication algorithm.
This algorithm chains bit shifts and conditional XORs.
"""
product = 0
# Iterate over all 8 bits of the multiplier 'b'
for i in range(8):
# Step 1: If the lowest bit of 'b' is 1, add 'a' to the product
# We use XOR for addition, as established earlier
if (b & 1) == 1:
product ^= a
# Step 2: Prepare 'a' for the next iteration by multiplying it by x
# Check if the highest bit of 'a' (x^7) is set before shifting
highest_bit_set = (a & 0x80) != 0
# Shift 'a' left by 1 (multiply by x), and mask it to keep it 8-bit
a = (a << 1) & 0xFF
# Step 3: Modulo reduction
# If the highest bit was set, 'a' just overflowed to x^8.
# We reduce it by XORing with the irreducible polynomial.
if highest_bit_set:
a ^= GaloisField256.REDUCTION_POLYNOMIAL
# Step 4: Shift 'b' right by 1 to process the next bit in the next loop
b >>= 1
return product
# --- Implementation Example ---
# Let's test multiplying 0x57 and 0x83. In standard math, this is massive.
# In GF(2^8), it perfectly wraps around to 0xC1.
result = GaloisField256.multiply(0x57, 0x83)
print(f"GF(2^8) Product: {hex(result)}") # Output: 0xc1
This code is the exact logic executed inside your CPU’s cryptographic hardware accelerators. It is highly efficient because bitwise shifts and XORs are the fastest instructions a processor can execute. There are no heavy floating-point division calculations stalling the pipeline.
9. Security Implications of Polynomial Math
Why do cryptographers insist on this specific polynomial arithmetic instead of just using prime integer fields like $GF(p)$? The answer comes down to hardware architecture and side-channel security.
If we used a prime number field—for example, $GF(251)$, which is the largest prime under 256—we would face two massive problems:
Step 1:
We would waste memory. A byte holds 256 values. If we cap our math at 251, the values 252, 253, 254, and 255 become illegal states. This causes data loss during encryption.
Step 2:
Integer modulo division is highly vulnerable to timing attacks. Calculating A % 251 takes a variable amount of time depending on how large A is. Hackers can measure these nanosecond timing differences in the CPU to extract the secret key (a side-channel attack).
By using addition in Galois field via XOR and multiplication via fixed-loop bit shifting, algorithms like AES run in “constant time.” Every byte, regardless of its value, takes the exact same number of CPU cycles to encrypt. This mathematical symmetry completely neutralizes timing attacks.
If you are interested in how this low-level arithmetic fits into the broader picture of network security, you can explore the official NIST FIPS 197 specification, or read our previous deep dive on how AES algorithm mathematics protect VPN traffic.
10. The Cryptographic Importance of Operations in Finite Fields
When studying operations in finite fields, it becomes clear why modern cybersecurity is so mathematically rigid. If developers attempted to build XOR encryption systems using standard integer math, the resulting ciphertext would be full of statistical biases. Hackers could easily analyze the frequency of the output bytes to reverse-engineer the original plaintext.
By enforcing strict polynomial arithmetic, the cipher guarantees that every single bit has a perfectly equal 50% chance of being a 0 or a 1 after the mathematical transformation. This is the true power of addition in Galois field. Because the XOR gate does not carry over bits to the next column (like standard decimal addition does, where 9 + 1 = 10), each bit is calculated completely independently.
This independence prevents mathematical “avalanches” from breaking the bounds of the 8-bit memory register. When you combine the absolute flatness of addition in Galois field with the non-linear wrapping of polynomial arithmetic multiplication (using the irreducible polynomial), you get a cryptographic primitive that is impervious to algebraic cryptanalysis. It is no exaggeration to say that the entire global financial system rests securely on these precise operations in finite fields.
11. Conclusion
The next time you write code that handles secure data, remember that underneath the high-level API calls, a beautiful and complex mathematical dance is occurring.
We have learned that standard computing math is utterly useless for cryptography due to unbounded memory limits and linear predictability. By transforming bytes into algebraic formulas, we enter the world of finite fields. Here, the simple hardware XOR gate becomes the engine of addition in Galois field, providing the unbreakable foundation for XOR encryption.
Meanwhile, polynomial arithmetic allows us to multiply bytes together, utilizing an irreducible prime polynomial to perfectly rebound overflows back into an 8-bit space. This is the absolute bleeding edge of digital defense, executed flawlessly millions of times a second by the device you are reading this on right now.
Bądź na bieżąco!
Zapisz się, aby nie przegapić nowości na Review Space.
Join Our Newsletter
No spam. Unsubscribe anytime.