Throughout our journey into historical cryptanalysis, we have seen a recurring theme: mathematics always wins. Whether it was the ancient Caesar shift falling to frequency analysis, or the mighty Enigma machine collapsing under the weight of electromechanical brute force and the Index of Coincidence, every cipher eventually surrendered. This historical arms race naturally led cryptographers to a profound question: is it mathematically possible to create a truly unbreakable cipher?
The answer is yes. It is called one-time pad cryptography (OTP). When implemented correctly, it is the only encryption method in existence that provides absolute, mathematically proven perfect secrecy. No matter how much computing power an attacker possesses—even if they harness the power of quantum computers—the one-time pad cannot be cracked.
In this final, comprehensive module on classical encryption, we will dissect the Vernam cipher mechanics, explore the deep logic of Claude Shannon perfect secrecy, analyze the Boolean logic of XOR encryption, and understand why this ultimate cryptographic weapon is both infinitely powerful and notoriously difficult to use in the real world.
1. The Architecture of the One-Time Pad
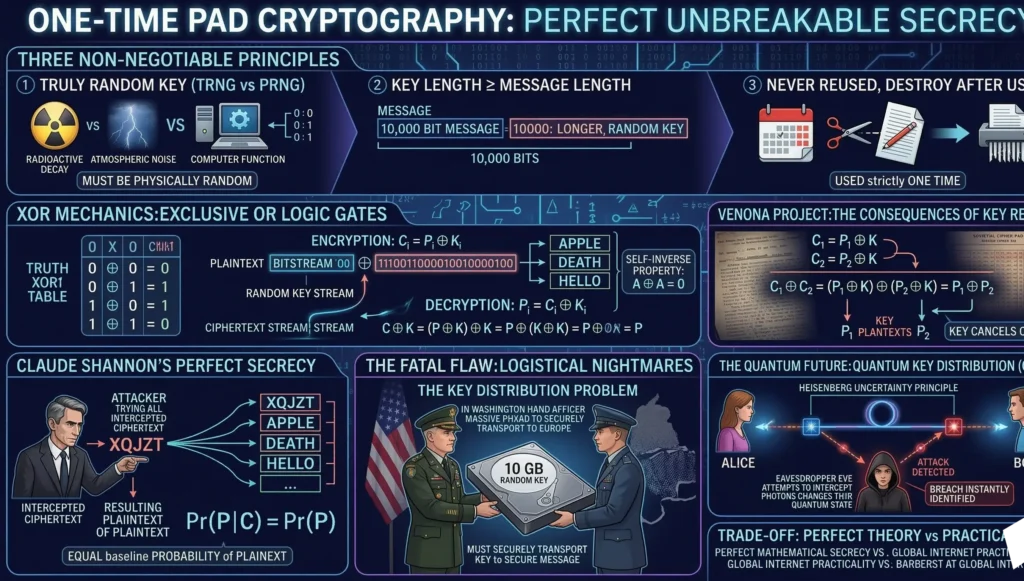
Invented in 1917 by Gilbert Vernam and Joseph Mauborgne, the architecture of one-time pad cryptography is deceptively simple. It operates as a continuous stream cipher but with three uncompromising, absolute rules that must never be broken under any circumstances:
- The key must be completely random: It cannot be generated by a mathematical algorithm or a predictable computer function. It must be derived from true physical entropy.
- The key must be at least as long as the plaintext: If the message is 10,000 bits long, the key must be exactly 10,000 bits long.
- The key must never be reused: It is used strictly one time to encrypt a single message, and then immediately destroyed by both the sender and the receiver.
If even one of these rules is slightly compromised, the unbreakable cipher mathematics instantly collapse, rendering the system completely vulnerable to modern statistical attacks.
2. The Deep Logic: XOR Encryption Mechanics
While early historical one-time pads used modular arithmetic on letters (similar to the Vigenère Tabula Recta), modern digital implementations of the Vernam cipher mechanics rely entirely on binary mathematics. Specifically, they utilize the Exclusive-OR (XOR) logic gate, denoted by the mathematical symbol $\oplus$.
To understand why XOR is the beating heart of digital cryptography, we must look at its Boolean logic truth table. The XOR operation compares two bits and outputs a $1$ only if the bits are different. If they are the same, it outputs a $0$.
- $0 \oplus 0 = 0$
- $0 \oplus 1 = 1$
- $1 \oplus 0 = 1$
- $1 \oplus 1 = 0$
The Mathematical Properties of XOR
The XOR encryption logic possesses several fundamental algebraic properties that make it perfect for cryptography:
- Commutativity: $A \oplus B = B \oplus A$
- Associativity: $A \oplus (B \oplus C) = (A \oplus B) \oplus C$
- Identity Element: $A \oplus 0 = A$ (XORing with zero leaves the original bit unchanged).
- Self-Inverse (The Magic Property): $A \oplus A = 0$ (XORing any value with itself destroys the value, resulting in zero).
The encryption process leverages these properties perfectly. To encrypt a plaintext bit ($P$) with a random key bit ($K$), we calculate the ciphertext bit ($C$):
$$C = P \oplus K$$
To decrypt the message, the receiver simply XORs the ciphertext with the exact same key. Watch how the self-inverse property restores the original data:
$$C \oplus K = (P \oplus K) \oplus K = P \oplus (K \oplus K) = P \oplus 0 = P$$
This absolute symmetry means the encryption algorithm and the decryption algorithm are exactly the same operation. It is computationally flawless.
3. Claude Shannon and the Proof of Perfect Secrecy
For decades, the OTP was believed to be secure purely by intuition, but it wasn’t until 1945 that legendary mathematician Claude Shannon rigorously proved it. During his classified work at Bell Labs during WWII, Shannon developed Information Theory and mathematically defined Claude Shannon perfect secrecy.
Shannon stated that a cipher achieves perfect secrecy if the ciphertext provides absolutely zero information about the plaintext. Mathematically, the probability of the plaintext $P$ given the ciphertext $C$ is exactly equal to the baseline, prior probability of the plaintext itself:
$$Pr(P|C) = Pr(P)$$
What does this mean in plain English? Imagine an attacker intercepts a 5-letter ciphertext: “XQJZT”. They possess infinite computing power and try every possible 5-letter key. The mathematics of the one-time pad guarantee that “XQJZT” will decrypt into every single 5-letter word in existence.
With one key, it decrypts to “APPLE”. With another, it decrypts to “DEATH”. With yet another, it decrypts to “HELLO”. Because the key is truly random, every resulting word is mathematically equally probable. The attacker has no statistical leverage, no Index of Coincidence, and no frequency decay curve to guide them. The ciphertext gives them zero information. This is the definition of unbreakable cipher mathematics.
4. The Entropy Problem: True Randomness vs Pseudorandomness
The mathematical perfection of the One-Time Pad hinges entirely on Rule #1: The key must be completely random. This brings us to a profound philosophical and computer science problem: computers are inherently deterministic machines. They cannot generate true randomness.
If you ask a standard programming language (like Python or C++) to generate a random key using a function like random(), it utilizes a Pseudorandom Number Generator (PRNG). A PRNG uses a mathematical formula and a starting “seed” to produce a sequence of numbers that looks random to humans, but is highly predictable to cryptanalysts.
If you encrypt a message using a pseudorandom key, you are not using one-time pad cryptography; you are using a standard stream cipher, which can be broken by reverse-engineering the PRNG’s internal state. To achieve Claude Shannon perfect secrecy, the key must be generated by a Hardware True Random Number Generator (TRNG). These devices extract entropy from unpredictable physical phenomena in the universe, such as:
- The decay of radioactive isotopes.
- Atmospheric electromagnetic noise.
- Quantum fluctuations of photons hitting a semi-transparent mirror.
In Shannon’s Information Theory, the entropy $H(X)$ of the key must be absolute and maximal, ensuring total unpredictability:
$$H(X) = – \sum_{i} P(x_i) \log_2 P(x_i)$$
5. The Fatal Flaw: The Key Distribution Problem
If the one-time pad is mathematically unbreakable and true randomness can be achieved with hardware, why isn’t it used to secure our daily internet banking, WhatsApp messages, or enterprise VPNs? The answer lies in the catastrophic logistical nightmare of its own rules.
Because the key must be exactly as long as the message and cannot be reused, you face the insurmountable Key Distribution Problem. If a military general in Washington wants to send a secure 10-gigabyte video stream to a commander in Europe, they first need to securely, physically transport a 10-gigabyte hard drive containing the completely random TRNG key to Europe.
But logically, if you already possess a completely secure channel to physically transport a 10-gigabyte key across the world without it being intercepted, why encrypt the video at all? You could just put the video itself on that hard drive. This paradox makes OTP useless for real-time global internet communication.
6. The Venona Project: When the Rules are Broken
The absolute security of the OTP only exists if humans follow the rules flawlessly. History has shown that humans are the weakest link in any cryptographic architecture. During the Cold War, Soviet KGB spies utilized printed one-time pads to communicate with Moscow. However, due to the intense pressure and logistical difficulties of manufacturing and secretly distributing completely random pads, Soviet operators made a fatal mistake: they reused some pages of their keypads.
This single human error shattered the unbreakable cipher mathematics. If two plaintexts ($P_1$ and $P_2$) are encrypted with the exact same key ($K$), an attacker can intercept the two ciphertexts ($C_1$ and $C_2$) and XOR them together.
$$C_1 \oplus C_2 = (P_1 \oplus K) \oplus (P_2 \oplus K) = P_1 \oplus P_2$$
Because $K \oplus K = 0$, the key completely cancels itself out! The attacker is left with the two plaintexts XORed against each other, which can be easily separated using natural language statistical analysis. By exploiting this exact mathematical flaw, American cryptanalysts in the VENONA project were able to read thousands of top-secret Soviet communications, leading to the exposure of major spy rings.
7. The Future: Quantum Key Distribution (QKD)
Will the One-Time Pad ever become practical? The answer might lie in quantum physics. Today, researchers are solving the Key Distribution Problem using Quantum Key Distribution (QKD). By sending polarized single photons over fiber optic cables, two parties can establish a completely random, shared key across vast distances.
Because of the laws of quantum mechanics (specifically the Heisenberg Uncertainty Principle), if a hacker tries to intercept the photons to copy the key, the quantum state of the photons collapses, instantly alerting the sender and receiver to the breach. QKD might finally allow humanity to use the One-Time Pad at scale, marrying quantum physics with Claude Shannon perfect secrecy.
Conclusion: The Ultimate Cryptographic Paradox
The One-Time Pad is the ultimate cryptographic paradox: mathematically perfect in theory, yet fundamentally impractical for our current globalized digital infrastructure. It forced the cybersecurity industry to accept a profound compromise.
Today, the algorithms that secure our digital lives—like Advanced Encryption Standard (AES) or RSA—do not use perfect secrecy. Instead, they rely on computational security. Modern encryption doesn’t rely on being mathematically unbreakable; it relies on being so mathematically complex that it would take the world’s fastest supercomputers billions of years to guess the key. We traded the absolute, theoretical perfection of the One-Time Pad for the practical functionality of the modern internet.the theoretical perfection of the One-Time Pad for the practical functionality of modern the internet.
Bądź na bieżąco!
Zapisz się, aby nie przegapić nowości na Review Space.
Join Our Newsletter
No spam. Unsubscribe anytime.