Blog
Explore our latest insights, news, and updates.
Cybersecurity Course
Dec 21
8 min
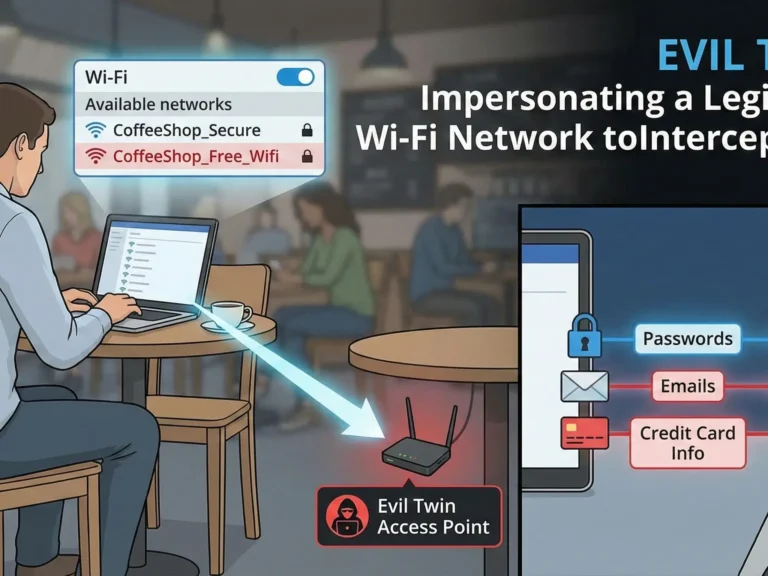
The Evil Twin Attack Explained: How Hackers Clone Wi-Fi Networks (And Why Your Phone Helps Them)
Introduction: Trust is a Vulnerability Imagine the scene. You walk into your favorite coffee shop. You order a…
Read More →

Cybersecurity Course
Dec 21
9 min
Cybersecurity 101: How the Internet Actually Works (and Why It’s Leaking Your Data)
Introduction: The Illusion of the Private Room Imagine you are sitting in your living room. The curtains are…
Read More →

Beauty & Fragrance
Dec 13
11 min
Empire of Medusa: Why Versace Smells of Luxury, Passion, and Danger
Introduction: More Than Just a Scent When you pick up a bottle of Versace, you aren’t just holding…
Read More →
Cybersecurity
Dec 11
3 min
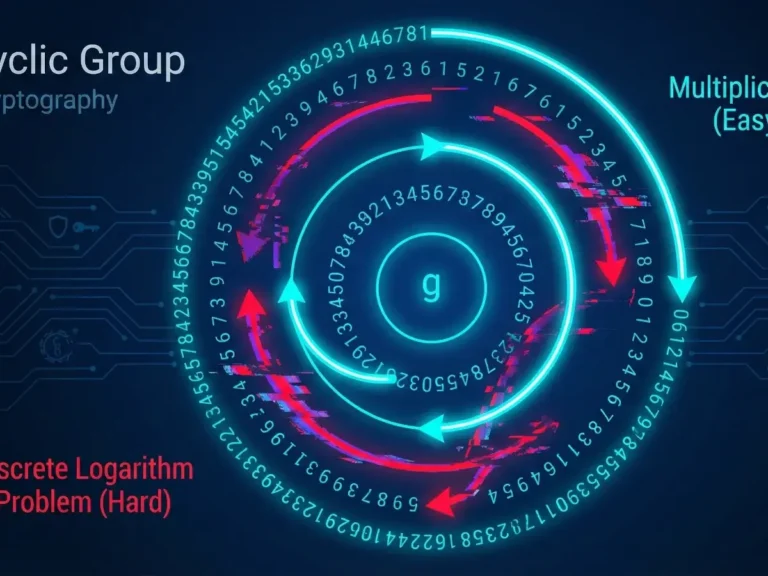
Cyclic Groups and the Discrete Logarithm: The Hard Math Behind Diffie-Hellman
We have explored Prime Numbers and Modular Arithmetic in previous articles. Now, we are ready to combine them…
Read More →
Cybersecurity
Dec 11
5 min
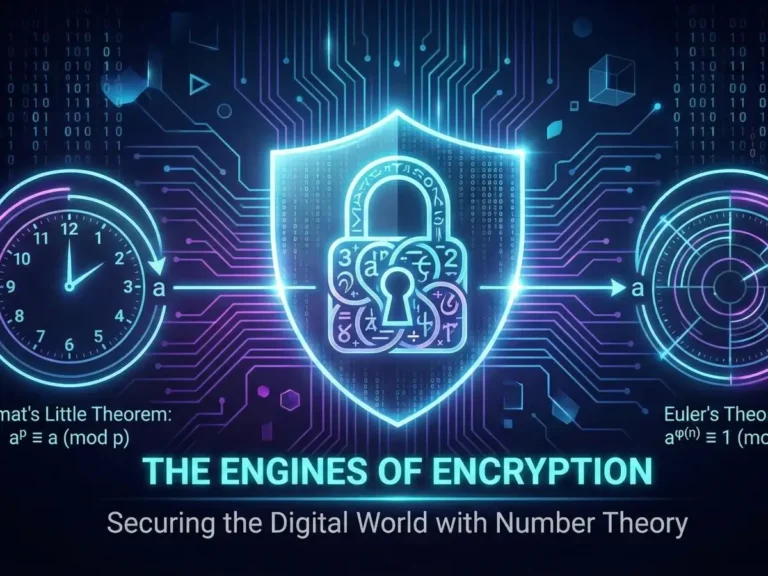
The Engines of Encryption: Fermat’s Little Theorem & Euler’s Theorem
If you have been following our series on the mathematics of cryptography, we have explored the “atoms” (Prime…
Read More →
Blog
Nov 29
4 min
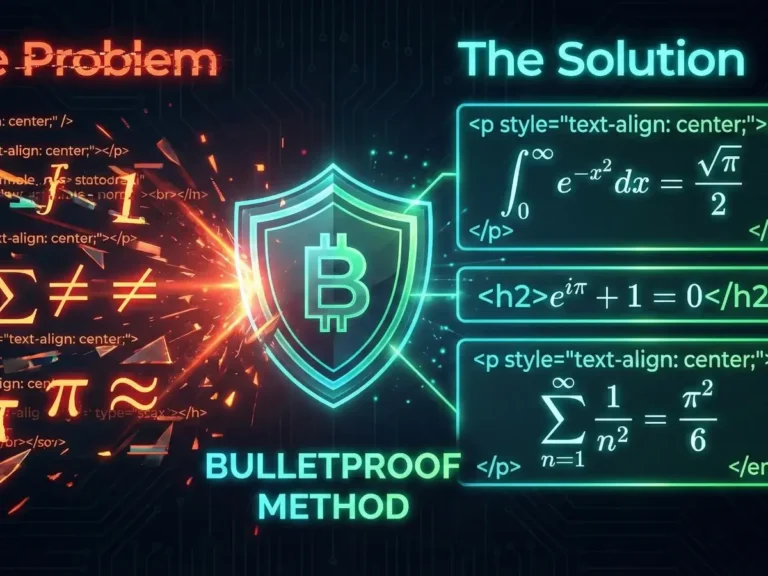
The “Bulletproof” Method: How to Write Mathematical Articles in WordPress (HTML + LaTeX)
If you have ever tried to publish a blog post containing complex mathematics, you know the struggle. Most…
Read More →