Blog
Explore our latest insights, news, and updates.
Cryptography
Mar 12
7 min
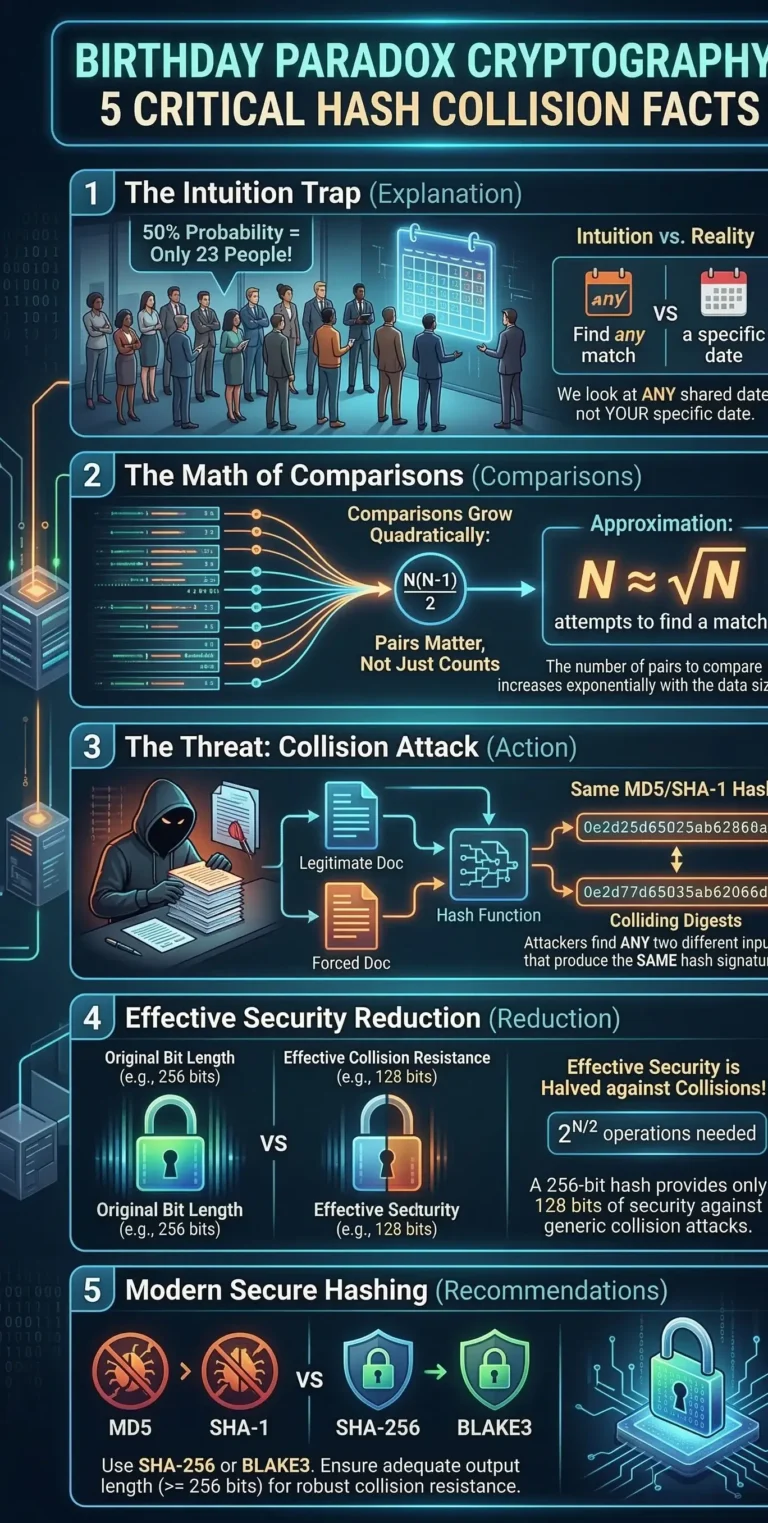
Birthday Paradox Cryptography: 5 Critical Hash Collision Facts
Birthday paradox cryptography is the absolute mathematical foundation for understanding how digital signatures, blockchain ledgers, and password storage…
Read More →
Cryptography
Mar 12
7 min
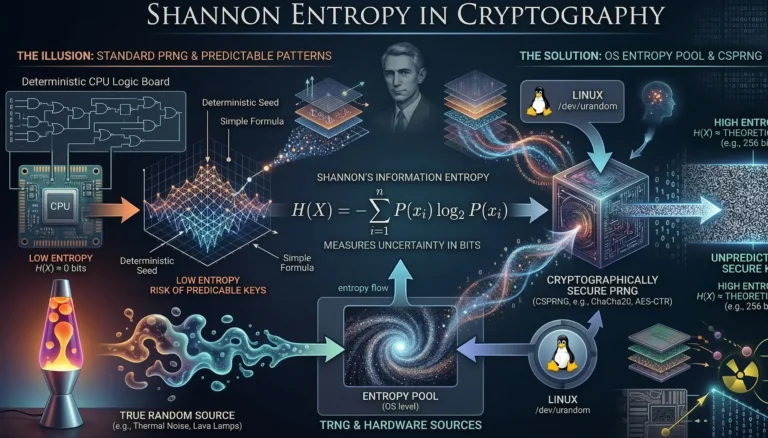
Shannon Entropy in Cryptography: 5 Critical Rules for Secure Keys
Understanding Shannon entropy in cryptography is not just an academic exercise; it is the absolute foundation of modern…
Read More →
Cryptography
Mar 10
9 min
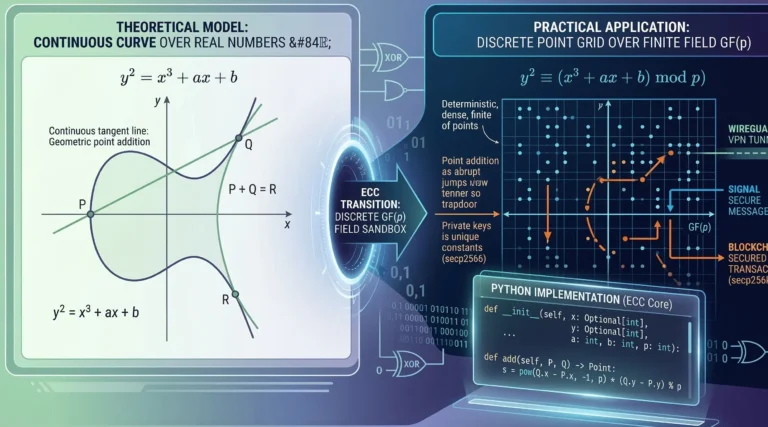
7 Brilliant Secrets of Elliptic Curve Cryptography & ECC
Finite Fields in Elliptic Curve Cryptography (ECC): From Theory to Practice Modern digital security is undergoing a fundamental…
Read More →
Cryptography
Mar 10
11 min
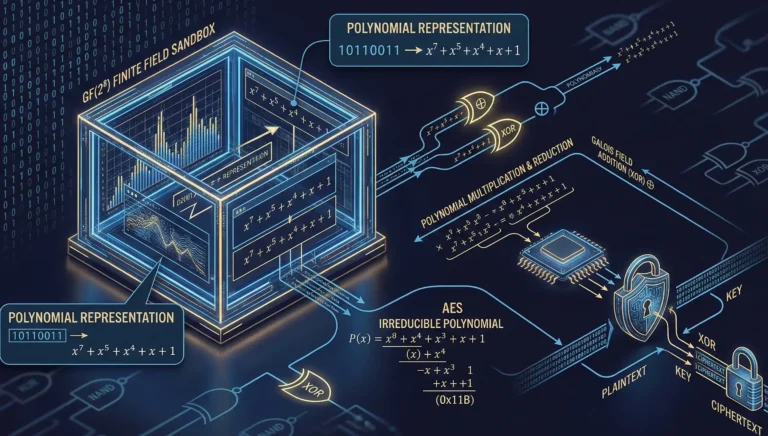
7 Brilliant Secrets of Operations in Finite Fields & XOR Encryption
Finite Field Arithmetic: How Computers Add and Multiply Bytes At the core of every secure digital communication—whether you…
Read More →
Cryptography
Mar 12
12 min
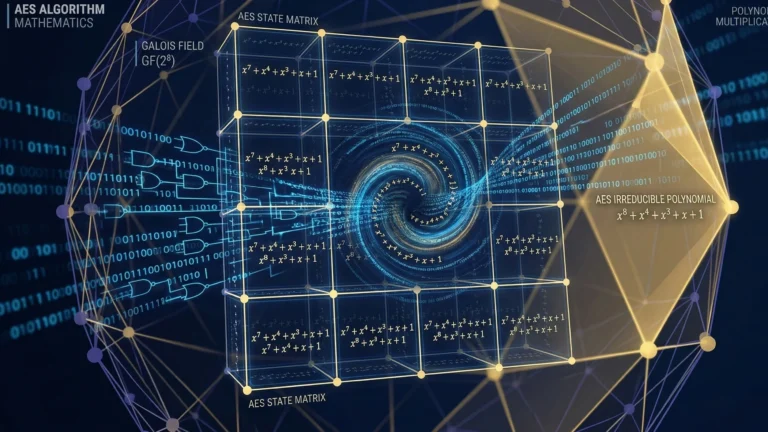
How AES Works: 5 Brilliant Secrets of Algorithm Mathematics
How AES Works: The Brilliant AES Algorithm Mathematics Explained If you have ever connected to a virtual private…
Read More →

Cryptography
Mar 8
10 min
Galois Fields Explained: 5 Amazing Secrets for Cryptography
Galois Fields Explained: 5 Amazing Secrets of Finite Fields in Cryptography If you write code for a living,…
Read More →