Understanding injective surjective bijective mapping is the absolute cornerstone of discrete mathematics and computer science. Now that we have established a solid foundation in Set Theory Operations, it is time to explore the dynamic relationships between these sets. A mapping (or function) from Set $X$ to Set $Y$ is a strict, unambiguous rule that demonstrates exactly how elements of the first set are assigned to the elements of the second.
However, not all mappings are created equal. Properly identifying an injective surjective bijective mapping allows mathematicians to determine if a process can be reversed or if data will be lost. Whether you are building a relational database, designing a cryptographic hash function, or proving the cardinality of infinite sets, you are actively relying on these core mathematical principles.
In this comprehensive guide, we will break down the strict mathematical definitions, provide algebraic proofs, analyze visual mapping diagrams, and explore how injective surjective bijective mapping governs the architecture of modern computing.
Why is Classification So Important?
When studying discrete mathematics, distinguishing the exact type of an injective surjective bijective mapping determines how sets relate to each other structurally. You can explore the foundational history and strict algebraic proofs of these relationships on highly authoritative resources like Wikipedia’s guide to mathematical functions or delve into deeper mathematical axioms at Wolfram MathWorld. These external resources confirm that without classifying functions correctly, modern computing simply would not work.
1. The Fundamental Anatomy of a Mathematical Function
Before diving into the specific types of mappings, we must define the anatomy of a function $f: X \to Y$. A function is a relation where every single element in the starting set is assigned to exactly one element in the target set. Let’s define the terminology:
- Domain (Set $X$): The complete set of all possible input values.
- Codomain (Set $Y$): The set of all potential output values. This is the universe where the arrows are allowed to land.
- Image / Range ($f(X)$): The specific subset of the codomain that actually gets hit by an arrow. The range is strictly the actual outputs.
- Pre-image: If $f(x) = y$, then $x$ is the pre-image of $y$.
The distinction between the Codomain and the Range is the secret key to understanding surjections, which we will explore shortly.
2. Deep Dive into Injective Mapping (One-to-One)
An injective mapping (often called a “one-to-one” function) is a strict function that preserves distinctness. It guarantees that no two different inputs will ever produce the same output.
The Formal Mathematical Definition
A function $f: X \to Y$ is injective if, for all $a, b \in X$:
$$f(a) = f(b) \implies a = b$$
Alternatively, using the contrapositive, it makes even more intuitive sense: If the inputs are different, the outputs must be different:
$$a \neq b \implies f(a) \neq f(b)$$
Cardinality Constraint (The Pigeonhole Principle)
For an injection to even be physically possible from Set $X$ to Set $Y$, the target set must have at least as many elements as the starting set. Mathematically, the cardinality must be $|X| \le |Y|$. If you have 5 pigeons (inputs) but only 4 holes (outputs), it is impossible to give each pigeon its own private hole. Two pigeons will be forced to share, destroying the injection.
Algebraic Proofs of Injection
Let’s prove whether the function $f(x) = 2x – 5$ mapping real numbers to real numbers ($f: \mathbb{R} \to \mathbb{R}$) is injective.
- Assume two outputs are equal: $f(a) = f(b)$.
- Substitute the function: $2a – 5 = 2b – 5$.
- Add 5 to both sides: $2a = 2b$.
- Divide by 2: $a = b$.
Because we mathematically arrived at $a = b$, we have successfully proven that $f(x) = 2x – 5$ is strictly injective.
Counterexample: Is $f(x) = x^2$ over $\mathbb{R} \to \mathbb{R}$ injective? No. Let’s take $x_1 = 3$ and $x_2 = -3$. Both $f(3)$ and $f(-3)$ equal $9$. Two different inputs hit the exact same output. On a graph, this fails the Horizontal Line Test, meaning a horizontal line drawn at $y=9$ intersects the parabola twice.
3. Deep Dive into Surjective Mapping (Onto)
A surjective mapping (often called an “onto” function) is a function of pure exhaustion. It guarantees that every single element in the target Set $Y$ is “hit” by at least one element from Set $X$. No element in the codomain is left behind.
The Formal Mathematical Definition
A function $f: X \to Y$ is surjective if, for every $y \in Y$, there exists at least one $x \in X$ such that:
$$f(x) = y$$
In simpler terms: The Range is exactly equal to the Codomain.
Cardinality Constraint
For a surjection to be possible, the starting set must have at least as many elements as the target set ($|X| \ge |Y|$). If you have 3 arrows to shoot (Set $X$) but 5 targets to hit (Set $Y$), it is mathematically impossible to hit every target. You will always leave some targets blank.
Algebraic Proofs of Surjection
Let’s evaluate $f(x) = x^2$ again, mapped from Reals to Reals ($f: \mathbb{R} \to \mathbb{R}$). Is it surjective?
To prove surjection, we set $y = x^2$ and solve for $x$: $x = \pm\sqrt{y}$.
Does this work for every real number $y$? No. If we choose $y = -4$ (which is in our codomain $\mathbb{R}$), we get $x = \sqrt{-4}$. In the realm of real numbers, you cannot take the square root of a negative number. Thus, $-4$ has no pre-image. The function is not surjective.
Note: If we simply redefine our codomain to only be non-negative real numbers ($f: \mathbb{R} \to [0, \infty)$), the same function suddenly becomes surjective! The defined universe matters.
4. Deep Dive into Bijective Mapping (Perfect Pairing)
A bijective mapping is the Holy Grail of functions. It represents a state of perfect, harmonious balance. A function is bijective if and only if it is both injective AND surjective.
The Characteristics of a Bijection
- Perfect 1-to-1 Match: Every input has a unique output (injection), and every output has exactly one input (surjection).
- Equal Cardinality: For finite sets, a bijection is only physically possible if both sets have the exact same number of elements: $|X| = |Y|$.
- Invertibility: This is the most crucial property. A function has an inverse $f^{-1}(y)$ if and only if it is a bijection. Because every arrow points to a unique target and no targets are empty, you can simply reverse the direction of all arrows, and it perfectly forms a valid new function going from $Y$ back to $X$.
Algebraic Proof of a Bijection
Let $f(x) = 3x + 2$ from $\mathbb{R} \to \mathbb{R}$.
1. Prove Injection:
$3a + 2 = 3b + 2 \implies 3a = 3b \implies a = b$. (It is injective).
2. Prove Surjection:
Let $y = 3x + 2$. Solving for $x$ gives us $x = \frac{y – 2}{3}$. Since any real number $y$ can be plugged into this equation to yield a valid real number $x$, every $y$ has a pre-image. (It is surjective).
Because it is both, $f(x) = 3x + 2$ is a bijection, and its inverse function is directly $f^{-1}(x) = \frac{x – 2}{3}$.
5. Visual Analysis: The Mapping Diagram Exam Problem
To ground this abstract theory, let’s analyze a classic discrete mathematics exam problem using a mapping diagram (Euler circles with arrows).
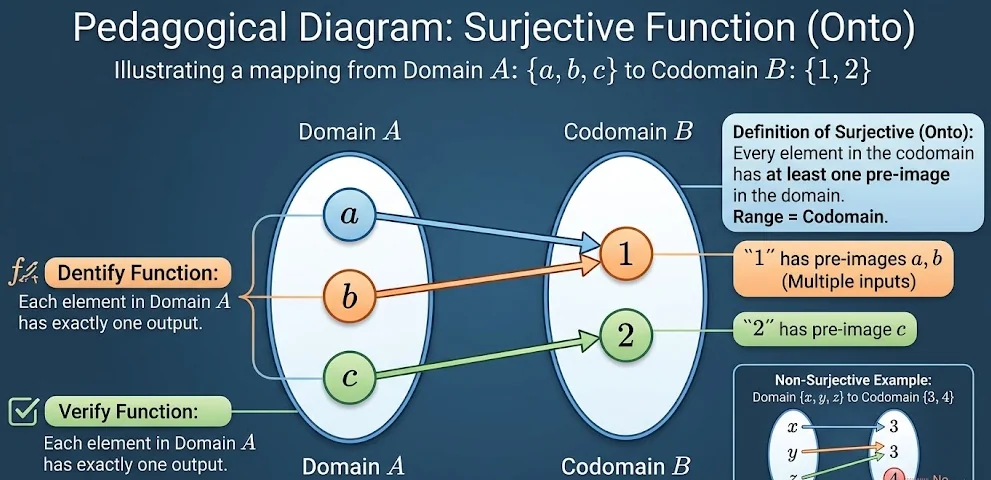
[Image of a set mapping diagram from domain A {a, b, c} to codomain B {1, 2} showing arrows: a->1, b->1, c->2]
The Data:
- Domain (Set $A$): $\{a, b, c\}$. (Cardinality = 3)
- Codomain (Set $B$): $\{1, 2\}$. (Cardinality = 2)
- The Mappings: $f(a) = 1$, $f(b) = 1$, $f(c) = 2$.
Evaluation and Verdict:
Test 1: Is this an Injection?
Verdict: FALSE. We must look at the target “1” in Set $B$. It is receiving arrows from both $a$ and $b$. Because $f(a) = f(b)$, the distinctness rule is broken. Multiple inputs lead to a single output. Therefore, it is not injective.
Test 2: Is this a Surjection?
Verdict: TRUE. We must look exclusively at Set $B$ and ask: “Are any elements left isolated without an incoming arrow?” The element “1” is hit. The element “2” is hit. The range $\{1, 2\}$ is perfectly equal to the codomain $\{1, 2\}$. Therefore, it is a surjective mapping.
Test 3: Is this a Bijection?
Verdict: FALSE. Because injective surjective bijective mapping theorems dictate that a bijection must pass both tests, failing the injection test automatically disqualifies it. Furthermore, because $|A| \neq |B|$ (3 is not equal to 2), a bijection is mathematically impossible from the start.
6. Crucial Applications in Computer Science
Why do software engineers and computer scientists obsess over the types of functions? Because these mathematical rules dictate how hardware and software manage data.
A. Cryptography and Hash Functions
When you store a password in a database, it is passed through a Hash Function (like SHA-256). A hash function takes an infinite number of possible passwords (Domain) and outputs a fixed-length string (Codomain). Because the domain is infinitely larger than the codomain, a hash function can never be injective (due to the Pigeonhole Principle). When two different passwords generate the exact same hash, it is called a Hash Collision. Cryptographers spend their lives trying to make these unavoidable collisions as statistically rare as possible.
B. Relational Databases (SQL)
When you design a database table for users, you create a Primary Key (like User_ID). The database engine strictly enforces an injective mapping between the User_ID and the actual User Record. If the database allowed two users to map to the same ID, data corruption would instantly occur. The mapping is one-to-one.
C. Lossless Data Compression
Algorithms like ZIP or FLAC rely heavily on bijective mappings. To compress a file, you map a large chunk of data to a smaller code. To decompress it, you must be able to read that code and perfectly recreate the original data without a single flipped bit. This requires a perfect, invertible two-way street—a mathematical bijection.
Conclusion
Understanding an injective surjective bijective mapping goes far beyond passing a discrete mathematics exam. It trains your brain to think about data constraints, edge cases, and mathematical reversibility. By mastering exactly how an injective surjective bijective mapping dictates the flow of information, you unlock a deeper understanding of modern algorithms, database architecture, and secure cryptographic networks.