Understanding differential cryptanalysis is the absolute pinnacle of modern cybersecurity engineering. In our previous modules, we explored how a lack of Shannon Entropy ruins key generation, how the Birthday Paradox forces hash collisions, and why ECB vs CBC mode determines the safety of structured data. However, what happens when your entropy is perfect, your hashes are long, and your CBC mode is flawless? Can a hacker still break the underlying block cipher itself?
The answer is yes—if the cipher’s internal mathematical structure is linear. Advanced threat actors do not waste time brute-forcing a 256-bit AES key; that would take millions of years. Instead, they look inside the algorithmic “black box” to observe how changing a single bit of the input text alters the output. By mapping these probabilities, they can reverse-engineer the secret encryption key.
In this definitive and highly advanced guide, we will explore the brutal mathematics of deciphering modern algorithms. We will provide a complete guide to having linear cryptanalysis explained, dive deep into the non-linear matrices of AES S-box mathematics, and prove why achieving perfect avalanche effect cryptography is the only way to build an unbreakable system.
1. The Fundamental Problem: Breaking the Black Box
A block cipher, at its core, is a mathematical function that transforms plaintext into ciphertext using a secret key. Naive developers assume that if the math is complicated enough, the cipher is secure. This is a fatal assumption.
If an algorithm consists solely of linear operations—such as addition, multiplication by a constant, or XOR ($\oplus$)—it can be broken instantly. Linear equations can be solved using basic linear algebra, no matter how many times you mix the data. Hackers exploit this by analyzing the relationship between the plaintext ($P$), the ciphertext ($C$), and the key ($K$).
To prevent this, cryptographers must inject artificial, mathematically rigorous chaos into the cipher. This chaos must destroy any predictable correlation between the input and the output. To understand how we build this defense, we must first understand the two most devastating mathematical attacks: linear and differential cryptanalysis.
2. Linear Cryptanalysis Explained: The Math of Probability
To get linear cryptanalysis explained properly, we must look at conditional probability. Discovered by Mitsuru Matsui in 1993, this attack attempts to find a linear approximation—a statistical bias—between subsets of plaintext bits, ciphertext bits, and key bits.
The attacker mathematically XORs specific bits of the plaintext and ciphertext together. In a perfectly secure cipher, the probability that this XOR equation equals $0$ or $1$ should be exactly $0.5$ ($50\%$). It should act like a perfectly fair coin toss.
However, if the cipher is flawed, the probability might be slightly biased, say $0.51$ ($51\%$). This deviation from $0.5$ is known as the linear bias. The fundamental mathematical expression for this approximation is:
$$P_i \oplus P_j \oplus \dots \oplus C_x \oplus C_y \oplus \dots = K_a \oplus K_b \oplus \dots$$
If an attacker can collect enough known plaintext-ciphertext pairs (often requiring millions of encrypted messages), they can leverage this tiny $1\%$ bias to calculate the probability of specific bits in the secret key. This is the core of having linear cryptanalysis explained: hackers do not guess the whole key at once; they statistically deduce it bit by bit by exploiting mathematical biases.
3. Differential Cryptanalysis: XOR Differences and Data Trails
While linear attacks look for biases across many unrelated texts, differential cryptanalysis (formalized by Eli Biham and Adi Shamir in the late 1980s) tracks the propagation of specific changes. It observes how a specific difference in the input affects the difference in the output.
Instead of one plaintext, the attacker takes two plaintexts ($P_1$ and $P_2$) that differ by only a few specific bits. The mathematical difference is calculated using the XOR operation:
$$\Delta P = P_1 \oplus P_2$$
The attacker feeds both plaintexts into the cipher and observes the XOR difference of the resulting ciphertexts ($\Delta C = C_1 \oplus C_2$). Because differential cryptanalysis operates on conditional probability, the attacker studies the internal rounds of the cipher to map a “differential characteristic.”
If the cipher is poorly designed, a specific input difference ($\Delta P$) will result in a specific output difference ($\Delta C$) with a probability significantly higher than random chance. By tracing this path of differences through the algorithm’s rounds, the attacker can extract the subkeys used during encryption. To defend against differential cryptanalysis, the algorithm must ensure that no input difference has a high probability of causing a specific output difference.
4. The Heart of AES: AES S-Box Mathematics
How do modern algorithms like the Advanced Encryption Standard (AES) defend against these statistical attacks? The answer lies in the only non-linear component of the AES algorithm: the Substitution Box, or S-box. Understanding AES S-box mathematics is the key to mastering modern encryption.
If AES only used XOR, shifting, and mixing, it would be a purely linear cipher and completely vulnerable. The S-box is designed specifically to shatter linearity. It takes an 8-bit input (a byte) and mathematically substitutes it with a completely different 8-bit output based on a strictly defined look-up table.
The core of AES S-box mathematics is rooted in Galois Field theory, specifically $GF(2^8)$. The transformation involves two critical mathematical steps:
- Multiplicative Inverse: Finding the inverse of the input byte within the Galois Field. This operation provides massive non-linearity, destroying any linear approximation attempts.
- Affine Transformation: Multiplying the result by a specific bit-matrix and XORing it with a constant vector (`0x63`). This step specifically prevents algebraic attacks and ensures that the output has no simple mathematical correlation to the input.
According to the official NIST FIPS 197 standard for AES, the S-box is meticulously engineered to minimize the maximum probability of any differential or linear bias. Because of perfect AES S-box mathematics, attackers cannot find a statistical foothold, rendering both linear and differential cryptanalysis mathematically infeasible against a full 10-round AES-128 cipher.
5. The Ultimate Defense: Avalanche Effect Cryptography
The ultimate goal of incorporating these complex S-boxes is to achieve a phenomenon known as the Strict Avalanche Criterion (SAC). This is the absolute gold standard of avalanche effect cryptography.
In nature, a single pebble can trigger a massive avalanche, completely altering the landscape. In avalanche effect cryptography, changing exactly one single bit in the plaintext input (or the encryption key) must cause a catastrophic cascade of changes, resulting in exactly $50\%$ of the output ciphertext bits flipping their value.
If changing 1 bit of input only changes 2 bits of output, the cipher has failed. The attacker can easily track the data flow. However, if changing 1 bit results in a $50\%$ probability of any given output bit flipping, the attacker is left staring at pure, unpredictable noise. Perfect avalanche effect cryptography ensures that the relationship between the plaintext and the ciphertext is so complex that no mathematical shortcut exists to reverse the process.
6. Practical Example: Anatomy of an AES Round
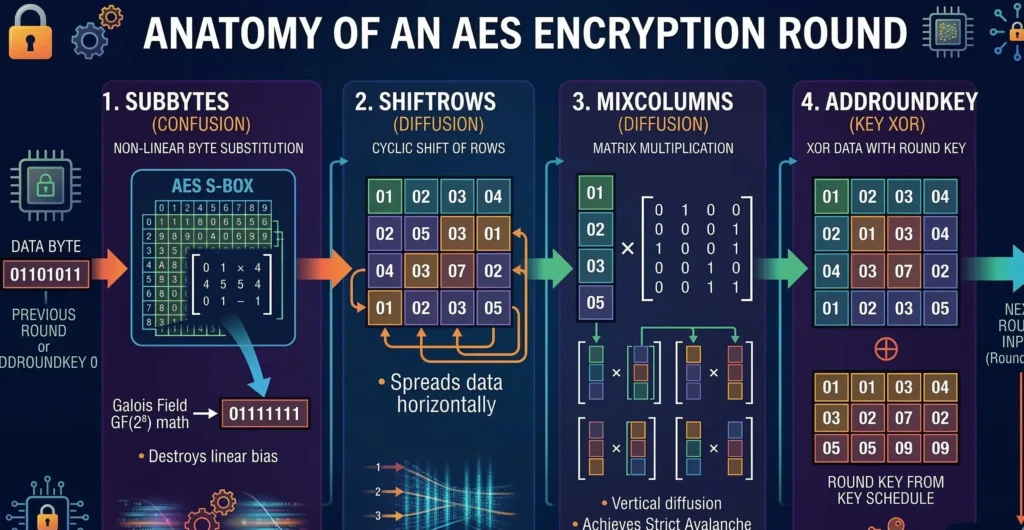
To see how differential cryptanalysis is defeated in practice, let’s look at the anatomical breakdown of a single AES encryption round. AES repeats this round 10, 12, or 14 times (depending on the key size). Each round consists of four highly specific layers designed to create confusion and diffusion:
- SubBytes (Confusion): This is where AES S-box mathematics is applied. Every single byte is replaced by its non-linear counterpart, destroying linear relationships.
- ShiftRows (Diffusion): The bytes are shifted across columns. This ensures that a change in one spot of the data block is spread horizontally.
- MixColumns (Diffusion): The data is mathematically multiplied by a matrix in the Galois Field. This provides vertical diffusion. Combined with ShiftRows, it guarantees the avalanche effect cryptography requirement within just two rounds.
- AddRoundKey: The data is XORed with a portion of the secret encryption key.
If an attacker attempts to inject a tiny XOR difference ($\Delta P$) into the first round, the SubBytes layer instantly scrambles the difference non-linearly. The ShiftRows and MixColumns layers then violently spread this scrambled difference across the entire 128-bit block. By the end of the second round, the original difference is completely untraceable, effectively neutralizing any attempt at differential cryptanalysis.
7. Conclusion: The Triumph of Mathematics
Modern cybersecurity is a continuous arms race between structural vulnerability and mathematical complexity. Without the profound insights gained from having linear cryptanalysis explained and studying the XOR distribution tables of differential cryptanalysis, we would still be using flawed ciphers today.
The enduring security of global financial systems, blockchain networks, and encrypted SaaS databases relies entirely on the robust non-linearity of AES S-box mathematics and the chaotic diffusion of avalanche effect cryptography. By understanding these advanced concepts, security architects can appreciate why algorithms like AES remain unbroken by classical computers, standing as the ultimate mathematical fortress against data breaches.
Bądź na bieżąco!
Zapisz się, aby nie przegapić nowości na Review Space.
Join Our Newsletter
No spam. Unsubscribe anytime.