Birthday paradox cryptography is the absolute mathematical foundation for understanding how digital signatures, blockchain ledgers, and password storage systems are eventually broken. While modern developers blindly trust algorithms like SHA-256 (used in Bitcoin) to secure billions of dollars, very few understand the statistical boundaries that dictate exactly when these algorithms will fail.
If you have read our previous deep-dive on Shannon Entropy and the flow of true randomness, you know that cryptography relies on vast, unpredictable numbers. But what happens when the universe of possible numbers simply runs out of room? The answer lies in the Pigeonhole Principle and the inevitable reality of data collisions.
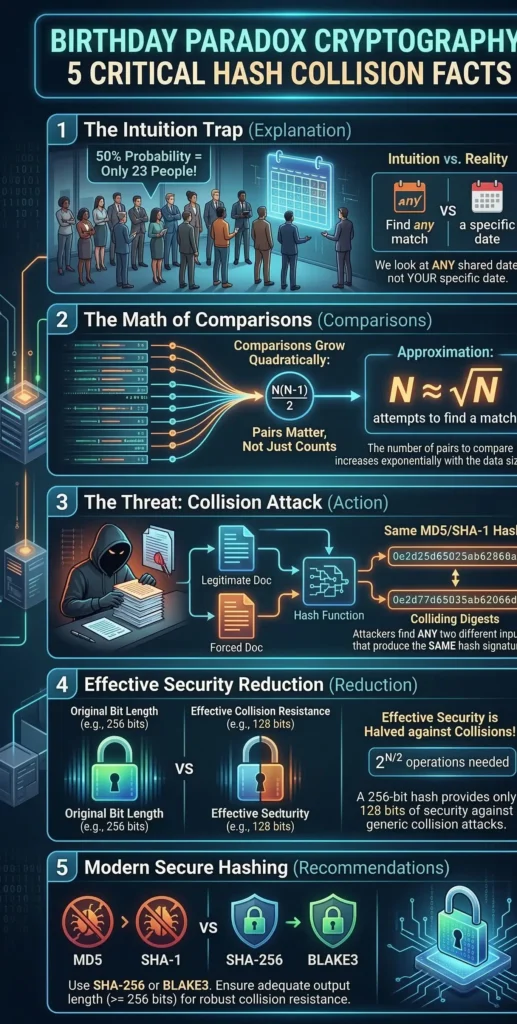
In this comprehensive module, we will explore the terrifying mathematics of coincidence. We will provide a complete birthday attack explanation, calculate the exact hash collision probability for modern algorithms, and examine why the catastrophic MD5 collision forced the entire cybersecurity industry to double their encryption standards.
1. The Core Problem: The Pigeonhole Principle in Hashing
Before diving into complex probability, we must define what a cryptographic hash function is. A hash function takes an input of any arbitrary size (a password, a PDF document, or a 100 GB database) and mathematically compresses it into a fixed-size output, known as a digest or hash.
For example, the SHA-256 algorithm will always output a 256-bit string. Mathematically, this means there are exactly $2^{256}$ possible unique hashes. While $2^{256}$ is a number vastly larger than the number of atoms in the observable universe, it is still a finite limit.
Because the number of possible inputs (infinite) is greater than the number of possible outputs (finite), the Pigeonhole Principle dictates that collisions are mathematically guaranteed. If you have 10 pigeons and 9 pigeonholes, at least two pigeons must share a hole. The critical cybersecurity question is not if a collision will happen, but how many attempts it will take to find one. This is where human intuition spectacularly fails.
2. The Mathematics of Coincidence: The 23 People Problem
If you ask a standard software engineer: “How many people do you need in a room to have a 50% chance that two of them share the exact same birthday?”, their intuition usually leads them to divide 365 days by 2, guessing around 180 people.
The mathematical reality is shockingly different: You only need 23 people.
This counter-intuitive truth is the engine behind birthday paradox cryptography. The cognitive flaw happens because humans tend to compare one specific person’s birthday to everyone else’s. But in a cryptographic collision attack, we don’t care who shares a birthday; we only care that any two people share one. We are comparing everyone to everyone.
With 23 people, we are not making 23 comparisons. We are looking at the combinations of pairs. The number of unique pairs is calculated as:
$$\frac{n(n-1)}{2} = \frac{23 \times 22}{2} = 253 \text{ pairs}$$
Because there are 253 independent chances for a match among 365 possible days, the probability crosses the 50% threshold. If you put 70 people in a room, the probability jumps to 99.9%. This exponential growth in probability is the ultimate weapon of cryptanalysts.
3. Calculating the Hash Collision Probability
Now, let’s map this logic from human birthdays to digital security. Instead of $d = 365$ days, a hash function has $d = 2^{L}$ possible outputs, where $L$ is the bit-length of the hash.
To calculate the hash collision probability ($P$), we use an exponential approximation derived from the Taylor series expansion. The formula to determine the probability of finding at least one collision after generating $n$ hashes in a space of $d$ possible outputs is:
$$P \approx 1 – e^{-\frac{n^2}{2d}}$$
Where:
- $P$ is the probability of a collision.
- $e$ is Euler’s number (approx. 2.718).
- $n$ is the number of generated hashes (the “people” in the room).
- $d$ is the total number of possible hashes (the “days” in the year).
When security engineers design new systems, understanding the exact hash collision probability is non-negotiable. If a database architect relies on a short hash to index millions of user records, the hash collision probability drastically increases with every new entry. This means that two different users might end up sharing the same database index, leading to critical data corruption or unauthorized access.
If we want to solve for $n$ (how many attempts we need to reach a 50% chance of a collision, where $P = 0.5$), the math simplifies to a terrifying boundary known as the Birthday Bound:
$$n \approx \sqrt{d}$$
4. The Birthday Attack Explanation: Why ^{256}$ Yields ^{128}$ Security
This mathematical simplification ($n \approx \sqrt{d}$) is the core of any birthday attack explanation. It proves that to break a hash function by finding any collision, an attacker does not need to compute all $2^{L}$ possibilities. They only need to compute $\sqrt{2^L}$, which is mathematically equal to $2^{L/2}$.
This effectively cuts the security level of any hash function exactly in half.
- A 128-bit hash algorithm gives you $2^{64}$ bits of security.
- A 160-bit hash algorithm (like SHA-1) gives you $2^{80}$ bits of security.
- A 256-bit hash algorithm (like SHA-256) gives you $2^{128}$ bits of security.
A proper birthday attack explanation must emphasize that hackers do not target specific users. Instead, they generate massive amounts of random data offline, waiting for any two hashes to match. This offline generation is the core of our birthday attack explanation, proving that system vulnerability depends entirely on the size of the cryptographic output space, not the complexity of the input.
This is precisely why Satoshi Nakamoto utilized SHA-256 for the Bitcoin protocol…
This is precisely why Satoshi Nakamoto utilized SHA-256 for the Bitcoin protocol. A security level of $2^{128}$ means a hacker would need to generate approximately $3.4 \times 10^{38}$ hashes to find a collision. Even if an attacker harnessed the combined computing power of the entire global NIST standard computing grid, it would take millions of years to reach this birthday bound.
5. The Death of Legacy Algorithms: The MD5 Collision
What happens when developers ignore the birthday bound? The answer is a catastrophic system failure, famously demonstrated by the death of the MD5 algorithm.
MD5 is a 128-bit hash function. According to birthday paradox cryptography, its collision resistance is only $2^{64}$ operations. While $2^{64}$ was a huge number in 1992 when MD5 was invented, by the mid-2000s, specialized GPU clusters could compute $2^{64}$ hashes in a matter of days.
The theoretical weakness became a global disaster when researchers successfully demonstrated a practical MD5 collision. The impact of a successful MD5 collision goes beyond just theoretical mathematics. When malware authors successfully execute an MD5 collision, they can forge digital certificates, making a dangerous virus appear as a legitimate software update from a trusted vendor. The most devastating real-world application of this attack was the Flame malware in 2012.
State-sponsored hackers used a chosen-prefix collision attack to generate a malicious Windows Update file that had the exact same MD5 hash as a legitimate Microsoft certificate. Because the MD5 hashes matched, the Windows operating system blindly trusted the file, allowing the malware to completely bypass all security protocols and infect high-level enterprise networks across the globe.
This incident forced the immediate deprecation of MD5 and SHA-1 across the entire software engineering industry, cementing the rule that any hash function with less than 256 bits is structurally unfit for digital signatures.
6. Practice: Simulating a Hash Collision in Python
To truly cement our birthday attack explanation, let’s write a Python script that actively hunts for a collision.
Because finding a collision in SHA-256 is practically impossible, we will intentionally weaken the algorithm by truncating its output to just 16 bits (2 bytes). According to the birthday paradox formula ($n \approx \sqrt{2^{16}}$), we should find a collision in just a few hundred attempts, rather than the 65,536 attempts intuition might suggest.
import hashlib
import os
def weak_hash(data: bytes) -> str:
"""
Creates an intentionally weak 16-bit hash by taking
only the first 4 hex characters of a SHA-256 digest.
"""
full_hash = hashlib.sha256(data).hexdigest()
return full_hash[:4] # 16 bits of security
def find_collision():
print("Starting Birthday Attack on 16-bit hash space...")
seen_hashes = {}
attempts = 0
while True:
attempts += 1
# Generate random data
random_data = os.urandom(16)
current_hash = weak_hash(random_data)
# Check if we have seen this hash before (The Birthday Paradox in action)
if current_hash in seen_hashes:
print(f"\n[!] COLLISION FOUND!")
print(f"Attempts needed: {attempts}")
print(f"Hash value: {current_hash}")
print(f"Input 1 (Hex): {seen_hashes[current_hash].hex()}")
print(f"Input 2 (Hex): {random_data.hex()}")
break
# Store the hash in our dictionary
seen_hashes[current_hash] = random_data
if __name__ == "__main__":
find_collision()
If you run this code, you will see output similar to this:
Starting Birthday Attack on 16-bit hash space...
[!] COLLISION FOUND!
Attempts needed: 312
Hash value: 7f8a
Input 1 (Hex): a1b2c3d4...
Input 2 (Hex): f9e8d7c6...
Notice the number of attempts: 312. We did not need to guess 65,000 times. Thanks to the combinatorial explosion of pairs, the collision was found almost immediately. This script is the ultimate proof of why cryptographic hash outputs must be massively long.
7. Conclusion: The Future of Hashing
The mathematics of birthday paradox cryptography prove that no digital fingerprint is entirely unique forever. The hash collision probability dictates that security is simply a game of buying time against the available computational power of your adversaries.
As computational power increases and quantum computing looms on the horizon, algorithms that seem impenetrable today will eventually suffer the same fate as the MD5 collision. Understanding the boundary of $\sqrt{d}$ allows security architects to stay one step ahead, ensuring that data integrity mechanisms remain unbroken.
In our next module, we will step away from hashes and delve into symmetric encryption. We will explore statistical cryptanalysis, discovering how attackers can read your encrypted database by simply looking at the visual patterns created by the Electronic Codebook (ECB) cipher mode.
Bądź na bieżąco!
Zapisz się, aby nie przegapić nowości na Review Space.
Join Our Newsletter
No spam. Unsubscribe anytime.