How AES Works: The Brilliant AES Algorithm Mathematics Explained
If you have ever connected to a virtual private network (VPN), made an online banking transaction, or sent an encrypted message on WhatsApp, your private data was protected by a single, globally trusted standard: the Advanced Encryption Standard (AES). As developers and IT professionals, we constantly implement libraries that handle symmetric-key encryption for us. We pass our plaintext and a secret key into a function, and out comes an unbreakable ciphertext. But what is actually happening inside that black box?
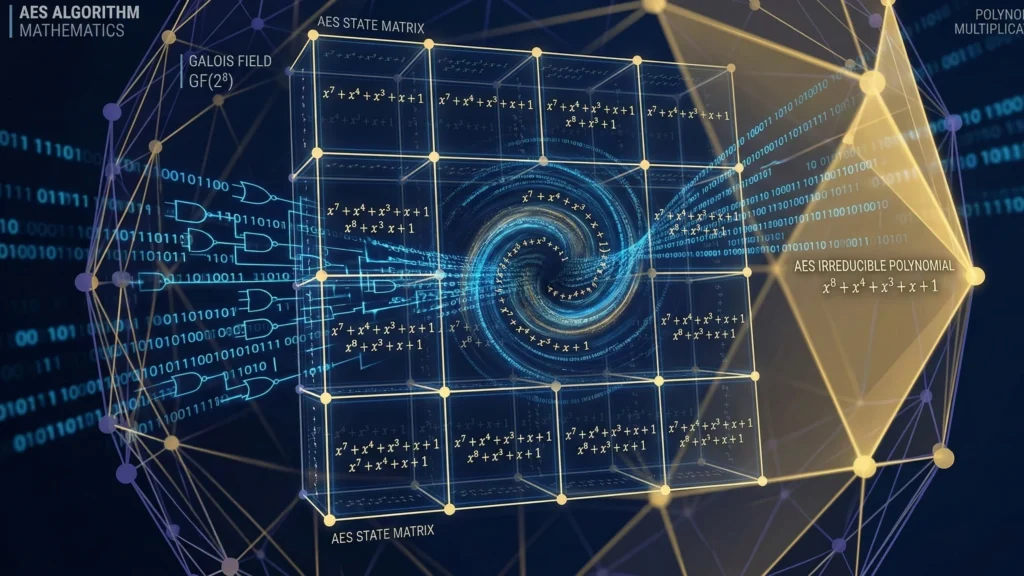
Many developers assume that encryption is just a chaotic blender of randomized bits. However, true cryptographic security is not built on chaos; it is built on perfectly structured, beautiful mathematics. When you look under the hood to deeply understand how AES works, you will not find random shuffling. Instead, you will discover AES algorithm mathematics—a strict, elegant system of polynomial arithmetic operating inside a finite mathematical universe known as a Galois Field.
In this ultimate deep-dive guide, we are going to break down the core of Galois fields in cryptography. We will look exactly at how your computer’s processor translates bytes of data into mathematical polynomials, performs arithmetic in the specific field GF($2^8$), and utilizes these block cipher mathematics to render your data mathematically impossible to crack.
1. The Black Box: How AES Works at a High Level
Before we dive into the deep mathematics, we must establish a high-level understanding of the AES architecture. AES is a symmetric-key algorithm, meaning the same secret key is used to both encrypt and decrypt the data. It was originally developed by Belgian cryptographers Joan Daemen and Vincent Rijmen (the Rijndael cipher) before being adopted by NIST.
AES does not encrypt your file all at once. It breaks your data into fixed-size chunks called “blocks.” Every block in AES is exactly 128 bits (16 bytes) long. These 16 bytes are arranged into a 4×4 grid known as the “State Matrix.”
During encryption, this State Matrix goes through a series of transformations called “Rounds” (10 rounds for AES-128, 14 rounds for AES-256). Each round consists of four distinct steps:
Step 1:
SubBytes: A non-linear substitution step where each byte is replaced with another according to a lookup table (the S-Box).
Step 2:
ShiftRows: A transposition step where the rows of the State Matrix are shifted cyclically.
Step 3:
MixColumns: A mixing operation which combines the bytes in each column of the state using matrix multiplication.
Step 4:
AddRoundKey: The matrix is combined with a sub-key derived from the main encryption key using a simple bitwise XOR.
While ShiftRows and AddRoundKey are trivial bit-shuffling and XOR operations, the true defensive power of AES relies entirely on SubBytes and MixColumns. Both of these steps are driven exclusively by the rigid rules of Galois fields in cryptography.
2. Why Standard Math Fails in Cryptography
To fully grasp AES encryption explained from a mathematical standpoint, we must ask: why can’t we just use regular multiplication to encrypt a byte?
Let’s say we have a byte of plaintext, which has a decimal value of 200. We want to encrypt it by multiplying it by a secret key byte, say 5. Using standard arithmetic, 200 × 5 = 1000.
The problem is immediate. A single byte in computer memory can only hold values from 0 to 255 (which is exactly 8 bits). The value 1000 requires at least 10 bits of memory. This is an overflow. If an algorithm allowed ciphertext to constantly grow in size with every operation, encrypting a 1-megabyte image would quickly consume gigabytes of RAM.
Furthermore, standard multiplication is highly linear and predictable. If hackers see that inputs are linearly related to outputs, they can use statistical cryptanalysis to reverse-engineer the secret key.
We need a mathematical system where we can add, subtract, multiply, and divide numbers, but the result never exceeds the 8-bit limit of a single byte. It must act as a perfect, closed loop. This is why we use finite fields, and specifically, the Rijndael finite field GF($2^8$).
3. Enter the Matrix: Galois Fields in Cryptography
As we covered in our foundational guides on abstract algebra, a Galois Field is a set with a finite number of elements where all arithmetic operations result in another element already inside the set. There are no fractions, no negative infinities, and no memory overflows.
The notation GF($2^8$) tells us exactly how this mathematical sandbox is built:
Base 2:
The base is 2, which perfectly aligns with binary logic. The only coefficients we use are 0 and 1.
Power 8:
The power is 8, meaning the field contains exactly 2⁸ = 256 elements. This maps perfectly to the 256 possible states of a standard 8-bit byte (from 00000000 to 11111111).
Representing Bytes as Polynomials
In AES algorithm mathematics, the computer does not view a byte as a normal integer (like 153). Instead, it views the byte as an algebraic polynomial. The bits of the byte, from left to right, represent the coefficients of the polynomial, from the highest power (x⁷) down to the lowest (x⁰).
Let’s take the binary byte 01010011 (which is 0x53 in hexadecimal). We write it out as a polynomial:
$$0x^7 + 1x^6 + 0x^5 + 1x^4 + 0x^3 + 0x^2 + 1x^1 + 1x^0$$
We drop all the terms with a zero coefficient, and we are left with a clean mathematical representation of our byte:
$$x^6 + x^4 + x + 1$$
By translating data into polynomials, AES can now perform extremely fast algebraic operations at the hardware level without ever treating the data as traditional numbers.
4. AES Addition: The Beauty of XOR
Let’s look at how we add two bytes together inside GF($2^8$). Suppose we want to add the byte 01010011 (which is x⁶ + x⁴ + x + 1) and the byte 11000010 (which is x⁷ + x⁶ + x).
In standard algebra, you would add the like terms. However, in our Galois field, the coefficients themselves belong to GF(2), meaning they can only be 0 or 1. If we add 1 + 1, it equals 2, which wraps around modulo 2 to become 0.
Therefore, addition in GF($2^8$) is performed modulo 2. Let’s add our polynomials:
Step 1: Write out the addition
The formula combines both polynomials.
$$(x^6 + x^4 + x + 1) + (x^7 + x^6 + x)$$
Step 2: Combine matching terms
Group the coefficients.
$$x^7 + (1+1)x^6 + x^4 + (1+1)x + 1$$
Step 3: Apply modulo 2
Since 1 + 1 = 0, the x⁶ and x terms cancel out entirely.
$$x^7 + x^4 + 1$$
If we convert this final polynomial back into binary, we get 10010001. If you are a programmer, you will immediately recognize what just happened. Adding two polynomials modulo 2 is the exact mathematical equivalent of the bitwise Exclusive-OR (XOR) operation.
This is why XOR is so heavily used in block cipher mathematics. It is the literal mathematical addition of Galois fields, allowing the CPU to execute it in a single, lightning-fast clock cycle.
5. Multiplication in GF(2⁸): The Irreducible Polynomial
While addition is simple, the true complexity of how AES works lies in multiplication. When we multiply two polynomials, the powers of x add together. If we multiply x⁶ by x³, we get x⁹.
But wait—an 8-bit byte can only hold terms up to x⁷. A term like x⁹ requires 10 bits of memory. This is the overflow problem we discussed earlier. To solve this, AES algorithm mathematics uses an irreducible polynomial.
Think of an irreducible polynomial as a prime number. Just as modulo arithmetic wraps around a prime integer, polynomial multiplication in GF($2^8$) wraps around an irreducible polynomial. The creators of AES selected this specific, mathematically proven polynomial for the standard:
$$P(x) = x^8 + x^4 + x^3 + x + 1$$
In hexadecimal, this is written as 0x11B. Whenever a multiplication operation results in a polynomial with a degree of 8 or higher, AES performs polynomial long division by P(x) and keeps only the remainder. This ensures the output always shrinks back down to a maximum of 8 bits.
The xtime Function
In software engineering, AES multiplication is implemented using a fundamental building block called xtime. The xtime operation represents multiplying a polynomial by simply x.
Multiplying by x is functionally equivalent to shifting all the bits in a byte to the left by one position (byte << 1).
However, if the leftmost bit of the byte was a 1 before the shift, shifting it left pushes it into the 9th bit position (creating an x⁸ term). When this overflow occurs, the algorithm must immediately XOR the shifted result with the AES irreducible polynomial (specifically the lower 8 bits of it, which is 0x1B).
By chaining these xtime shifts and XOR additions together, processors can securely multiply any two bytes in GF($2^8$) rapidly, avoiding heavy mathematical division at runtime.
6. The Heart of AES: SubBytes and the Extended Euclidean Algorithm
Now that we understand polynomial arithmetic, we can explore the most critical component of how AES works: the Substitution Box, or S-Box. This step occurs during the SubBytes phase of every AES round.
The S-Box is the only non-linear step in the entire AES algorithm. If AES were purely linear (just shifting and XORing), a hacker could easily solve it using simple systems of linear equations. The S-Box introduces deep mathematical chaos, effectively shutting down differential cryptanalysis attacks.
How does the S-Box generate this chaos? It relies on finding the multiplicative inverse of a polynomial in GF($2^8$). Finding the inverse of a byte a means finding another byte a⁻¹ such that:
$$a(x) \cdot a^{-1}(x) \equiv 1 \pmod{P(x)}$$
Finding the Inverse: The Extended Euclidean Algorithm
Computers cannot simply “guess” the inverse out of 256 possibilities efficiently. Instead, cryptographers use the Extended Euclidean Algorithm (EEA) for polynomials.
The EEA takes our input polynomial a(x) and the irreducible AES polynomial P(x). Because P(x) is irreducible (prime), the greatest common divisor between them is always 1. The algorithm iteratively works backward to express this 1 as a combination of a(x) and P(x):
$$s(x) \cdot a(x) + t(x) \cdot P(x) = 1$$
When we apply modulo P(x) to this equation, the t(x) · P(x) term becomes zero, leaving:
$$s(x) \cdot a(x) \equiv 1 \pmod{P(x)}$$
Therefore, the polynomial s(x) calculated by the algorithm is the exact multiplicative inverse a⁻¹. This calculation is heavily non-linear. An input of 00000001 might result in an inverse of 00000001, but 00000010 produces 10001101. The output bears no visible linear relationship to the input.
The Affine Transformation
To prevent hackers from exploiting the algebraic structure of the Galois field itself, AES applies an affine transformation to the inverse byte. This involves a matrix multiplication over GF(2) followed by an XOR with a constant vector (0x63).
These two steps (Extended Euclidean inversion + Affine transformation) create the S-Box. While libraries pre-calculate these values into a static lookup table for speed, you now know that the table is not random—it is a rigid, flawless manifestation of AES algorithm mathematics.
7. The Hidden Math: AES Key Schedule and Rcon
Galois fields in cryptography are not just used to scramble the plaintext; they are also heavily used to scramble the encryption key itself.
When you provide a 128-bit key to AES, it doesn’t just use that same key for all 10 rounds. It uses a Key Expansion Algorithm (Key Schedule) to generate 10 unique sub-keys. If AES didn’t do this, a vulnerability in one round could compromise the entire cipher.
To ensure each sub-key is radically different, AES introduces a Round Constant (Rcon). The Rcon is not a random number; it is mathematically derived directly from GF($2^8$).
Specifically, the Round Constant for round i is the polynomial x raised to the power of i – 1 in the Galois Field:
$$Rcon[i] = x^{i-1} \pmod{P(x)}$$
Step 1:
Round 1 Rcon is x⁰ = 1 (0x01).
Step 2:
Round 2 Rcon is x¹ = x (0x02).
Step 3:
Round 3 Rcon is x² (0x04).
Step 4:
By Round 9, x⁸ overflows the 8-bit limit, so the algorithm reduces it using the irreducible polynomial P(x), resulting in 0x1B.
By injecting these Galois Field powers into the key generation, AES guarantees that every single round key is mathematically distinct, preventing symmetry attacks.
8. MixColumns: The Ultimate Mathematical Scrambler
If the SubBytes step is designed to create confusion, the MixColumns step is designed to create “diffusion.” Diffusion ensures that changing a single bit in your original plaintext file will completely flip and alter at least half the bits in the final ciphertext.
MixColumns treats each column of the 4×4 State Matrix as a polynomial with 4 terms, and multiplies it by a fixed transformation matrix. Every single multiplication inside this matrix is performed under the strict rules of GF($2^8$).
The fixed transformation matrix used by AES is:
$$\begin{bmatrix} 02 & 03 & 01 & 01 \\ 01 & 02 & 03 & 01 \\ 01 & 01 & 02 & 03 \\ 03 & 01 & 01 & 02 \end{bmatrix}$$
Let’s say a column in our State Matrix consists of the bytes s₀, s₁, s₂, s₃. To find the new, mixed top byte (s’₀), the algorithm performs a dot product between the first row of the matrix and the column vector:
$$s’_0 = (02 \cdot s_0) \oplus (03 \cdot s_1) \oplus (01 \cdot s_2) \oplus (01 \cdot s_3)$$
Let’s break down this AES algorithm mathematics:
Step 1:
Multiplying a byte by 01 leaves it unchanged.
Step 2:
Multiplying a byte by 02 means we are multiplying the polynomial by x. This is exactly the xtime operation we defined earlier.
Step 3:
Multiplying a byte by 03 means we are multiplying by (x + 1). Mathematically, this is calculated by doing xtime(byte) ^ byte.
Step 4:
Finally, the addition operations ($\oplus$) are simply bitwise XORs tying all four mixed bytes together.
By heavily relying on 01, 02, and 03 in the matrix, the creators of AES ensured that MixColumns could be executed entirely through rapid CPU bit-shifting and XOR operations, keeping the encryption blazing fast while ensuring mathematically perfect data scrambling.
9. Writing the Math: AES Galois Field in Python
To truly cement how AES works, we must translate this theory into code. As an IT professional, writing a basic GF($2^8$) multiplier will demystify the AES algorithm mathematics forever.
Below is a clean Python implementation that can multiply any two bytes (a and b) exactly as the AES hardware instruction sets do it, wrapping around the irreducible polynomial 0x11B.
def gf_multiply(a, b):
"""Multiplies two bytes in the Galois Field GF(2^8) used by AES"""
p = 0 # This will hold the accumulated product
for i in range(8): # We loop through the 8 bits
# If the lowest bit of 'b' is 1, we add 'a' to our product via XOR
if (b & 1) != 0:
p = p ^ a
# We need to shift 'a' left (multiply by x) for the next bit of 'b'
# First, we check if shifting 'a' will cause an overflow
high_bit_set = (a & 0x80) != 0
a = (a << 1) & 0xFF # Shift left and ensure it stays 8-bit
# If an overflow happened, we reduce via the AES polynomial (0x1B)
if high_bit_set:
a = a ^ 0x1B
# Shift 'b' right to process the next bit in the next iteration
b = b >> 1
return p
# Let's test it with the AES MixColumns example:
# Multiplying byte 0x57 by 0x13 in GF(2^8)
result = gf_multiply(0x57, 0x13)
print(f"Result in hex: {hex(result)}") # Output will be 0xfe
This simple script represents the beating heart of internet security. Every time a secure packet leaves your router, millions of these polynomial multiplications are executed in parallel inside your device’s CPU.
10. Why AES Algorithm Mathematics Replaced Older Standards
To fully grasp how AES works, it is helpful to compare it to its predecessor, the Data Encryption Standard (DES). DES relied on older, simpler logical shifts and permutations that eventually became vulnerable to brute-force attacks as computing power increased. In contrast, the creators of AES built their cipher on the virtually unbreakable foundation of Galois fields in cryptography.
When the National Institute of Standards and Technology (NIST) officially published the AES specification in their FIPS 197 document, they validated that using AES algorithm mathematics operating strictly inside GF($2^8$) was the definitive solution for global data protection. This mathematical sandbox ensures that no matter how much quantum computing power hackers throw at the cipher, the algebraic non-linearity of the S-Box remains secure.
If you are building your own secure applications or configuring enterprise VPNs, understanding exactly how AES works at this granular mathematical level is crucial. We highly recommend continuing your education by reading our foundational guide on abstract algebra for programmers, which dives deeper into the rings and groups that make Galois fields in cryptography possible.
Whether you are analyzing secure network handshakes or developing custom encryption tools, mastering the operations of GF($2^8$) and the brilliant AES algorithm mathematics will elevate you from a standard coder to a true cybersecurity expert.
11. Conclusion: The Elegance of Digital Security
When most people think of cyber defense, they imagine heavy steel vaults, firewalls, and complex monitoring software. But as we have explored in this deep dive into Galois fields in cryptography, the ultimate shield is actually an invisible layer of abstract algebra.
To summarize the mastery of how AES works:
Step 1:
AES avoids standard arithmetic, which would cause massive memory overflows and expose statistical patterns to hackers.
Step 2:
It translates every 8-bit byte of your data into a mathematical polynomial residing in the Rijndael finite field GF($2^8$).
Step 3:
During the SubBytes phase, AES performs an intense non-linear substitution by calculating the exact multiplicative inverse of your data’s polynomial via the Extended Euclidean Algorithm, destroying linear vulnerabilities.
Step 4:
During the MixColumns phase, AES uses rapid bit-shifting (the xtime operation) to multiply state matrices, spreading the encryption influence of a single bit across the entire block.
Understanding AES algorithm mathematics elevates you from a developer who merely calls an API, to an engineer who understands the fundamental fabric of digital trust. The mathematics of AES are so robust that even if hackers captured all the supercomputers currently on Earth, they could not crack a single mathematically sound AES-256 session.
If you want to continue your journey into the mathematics of cyber defense, be sure to read our comprehensive guides on public-key infrastructure and how secure session tokens leverage these encrypted payloads to authenticate users on the modern web.
Bądź na bieżąco!
Zapisz się, aby nie przegapić nowości na Review Space.
Join Our Newsletter
No spam. Unsubscribe anytime.